Manage SSL Certificates
1. Overview
SSL certificates can be created, discovered, and stored in the centralized repository of Key Manager Plus, and requests can be raised for new certificates or domain addition to an existing certificate. Moreover, you are notified when a certificate is about to expire to help you with their timely renewal.
Use Key Manager Plus to:
- Create, discover, or import self-signed or CA issued certificates in the network.
- Generate Certificate Signing Request (CSR).
- Add requests for new certificates or adding a sub domain to an existing certificate.
- Receive notifications when certificates are about to expire.
Self-signed certificates and CSRs can be generated using RSA / DSA / EC key algorithms and SHA signature algorithm as per the details below:
- RSA – 1024, 2048, or 4096 bit keys; & SHA-2 (256, 384, or 512 bit) signature
- DSA – 512, or 1024 bit keys; & SHA-1 (160 bit) signature
- EC – 128, or 256 bit keys; & SHA-2 (256, 384, or 512 bit) signature
2. Discover Certificates in your Network
You can automatically discover all the certificates available in your network using Key Manager Plus, irrespective of the CA. You can discover the certificates anytime as needed or periodically based on scheduled tasks. The discovery options are quite flexible - you can discover certificates from a single server or multiple servers, and from multiple ports, at one go.
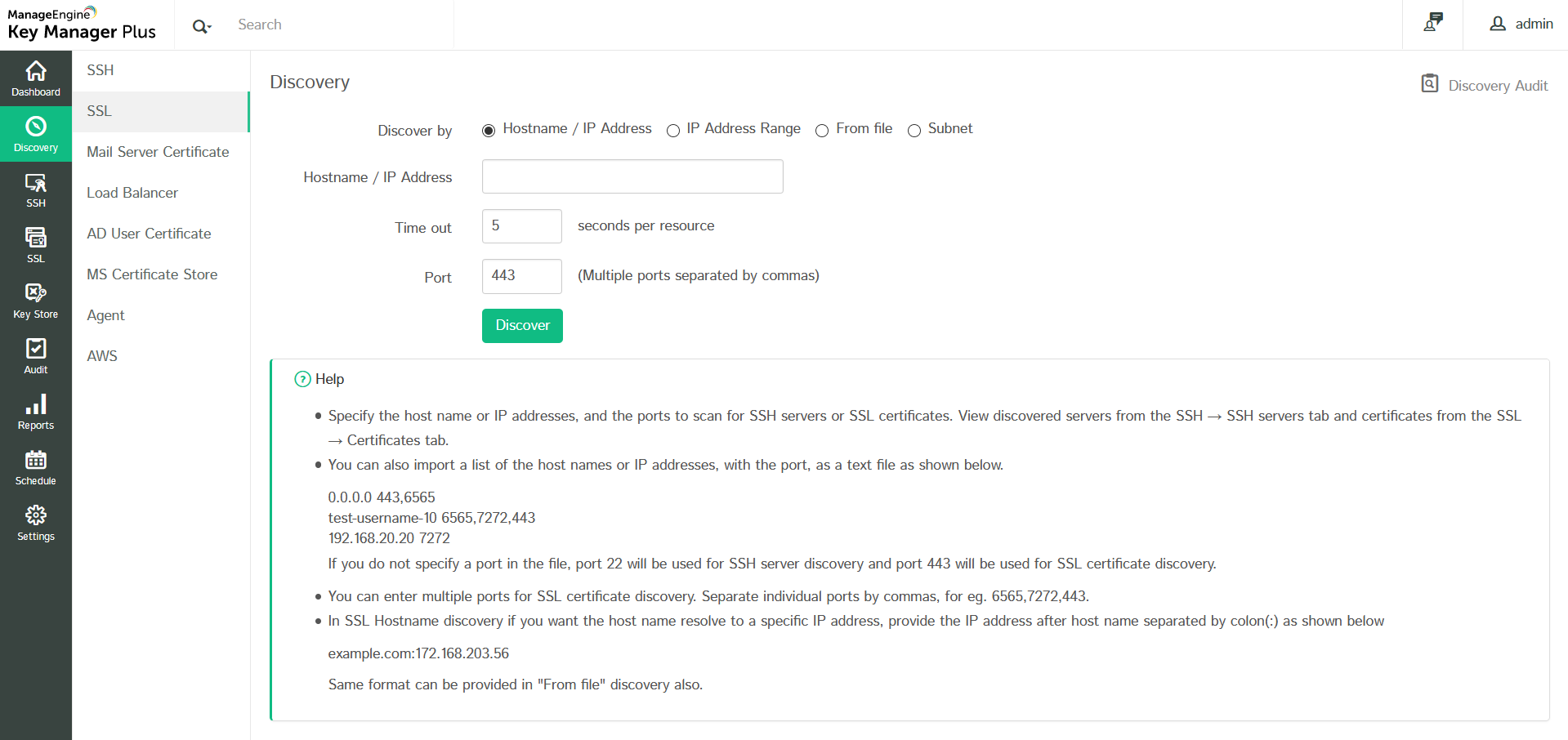
2.1 Discover SSL Certificates On Demand
To discover the certificates manually:
- Go to the Discovery tab in the GUI.
- Click the SSL tab.
- Select an option for the type of discovery.
- Hostname/IP address – Enter the name or IP address of the server from which the SSL certificates are to be discovered.
- IP address range – Specify an IP range and discover all the SSL certificates available in the servers falling under the range.
- From file – If you have a list of the servers in which certificates are available in your network saved as a text file, it can be loaded directly and all these certificates can be discovered.
- Subnet – You can also choose to discover resources from specific subnet works within an IP range using this option.
- In SSL Hostname discovery, if you want the host name to resolve to a specific IP address, provide the IP address after host name separated by colon (:) as shown below example.com:172.168.203.56. Same format can be provided in "From file" discovery as well.
Note: The file to be imported must be a text file containing the hostname or IP addresses of individual servers, entered on separate lines. Enter the ports to scan on each server separated by a space, entered on separate lines as illustrated below:
0.0.0.0 6565
test-username-10 443
192.168.20.20 7272
If you do not specify any port, SSL certificates using the default port 443 will be discovered.
- For bulk discovery using IP address range and Subnet options, there is an Exclude IP Address field that allows you to exclude specific resources from being discovered. Specify the IP addresses of the resources that need to be excluded one below another.
- Specify values for the Time out and the Port options.
- Time out: Refers to the number of seconds the application tries to discover the certificates (each). The default value is 5 seconds.
- Port: It refers to the port on the end terminal used for SSH communication. Port 443 is used by default for SSL certificates.
Note:
- You can specify multiple ports for the discovery of SSL certificates in a single discovery instance, separated by commas.
- During SSL discovery or when manually adding certificates to Key Manager Plus repository, you can choose to exclude specific certificates by providing their details (common name and serial number) in the Settings >> SSL >> Excluded Certificates tab.
Click the Discover button.When you click the Discover button, you will be redirected to the Discovery Status page where the status of the current discovery instance is updated.
2.2 Discover SSL Certificates Automatically through Schedules
SSL Certificate discovery can also be scheduled to occur at periodic intervals.
- Click the Schedule tab in the GUI.
- Click the Add Schedule button.
- In the Add Schedule window, enter a Name for the schedule and select the Schedule Type as SSL Discovery.
- Specify the Start and End IP addresses and the Port on the end terminal to check for SSL certificates.
- Select the Recurrence Type – hourly, daily, weekly, monthly, or once only. Set the Starting Time, Date or Day corresponding to the option chosen.
- Enter the email addresses of the users to be notified. The email settings can be configured from the Settings >> Mail Server Settings tab.
- Click the Save button.
You will get a message confirming addition of a new schedule.
The result of the schedule execution will get updated in the Schedule audit and the Discovery audit tabs.
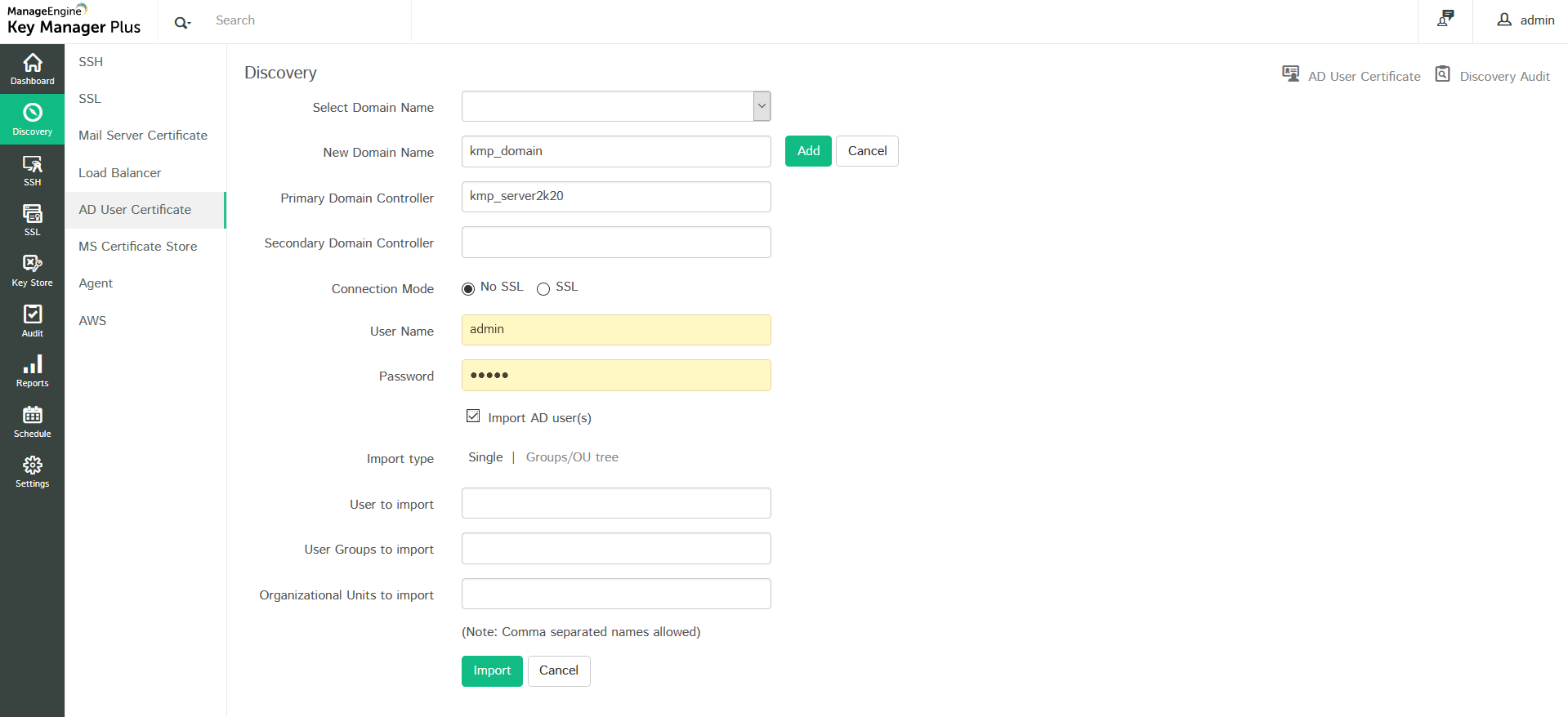
2.3 Discover Certificates Mapped to User Accounts in Active Directory
Key Manager Plus helps you discover and manage the certificates mapped to user accounts in Active Directory.
To perform AD user certificate discovery,
- Navigate to Discovery >> AD User Certificate.
- Select the required Domain Name, which forms part of the AD from the drop-down.
- Specify the DNS name of the domain controller. This domain controller will be the Primary Domain Controller.
- In case, the Primary Domain Controller is down, Secondary Domain Controllers can be used. If you have Secondary Domain Controllers, specify their DNS names in comma separated form. One of the available secondary domain controllers will be used. When you use SSL mode, make sure the DNS name specified here matches the CN (common name) specified in the SSL certificate for the domain controller.
- Enter a valid user credential (User Name and Password) of an user account within the particular domain. Then enter the users / user groups / OUs in which you want to perform the certificate discovery and click Import. To perform certificate discovery for groups/OUs as a whole, choose Groups/OU tree import type and select the required groups from the drop down list.
- Key Manager Plus also provides an option to import AD users while performing the certificate discovery. Enable the check box Import AD users to import those AD user accounts into Key Manager Plus for which the certificate discovery is done.
- The discovered certificates automatically get added to the certificate repository of Key Manager Plus.
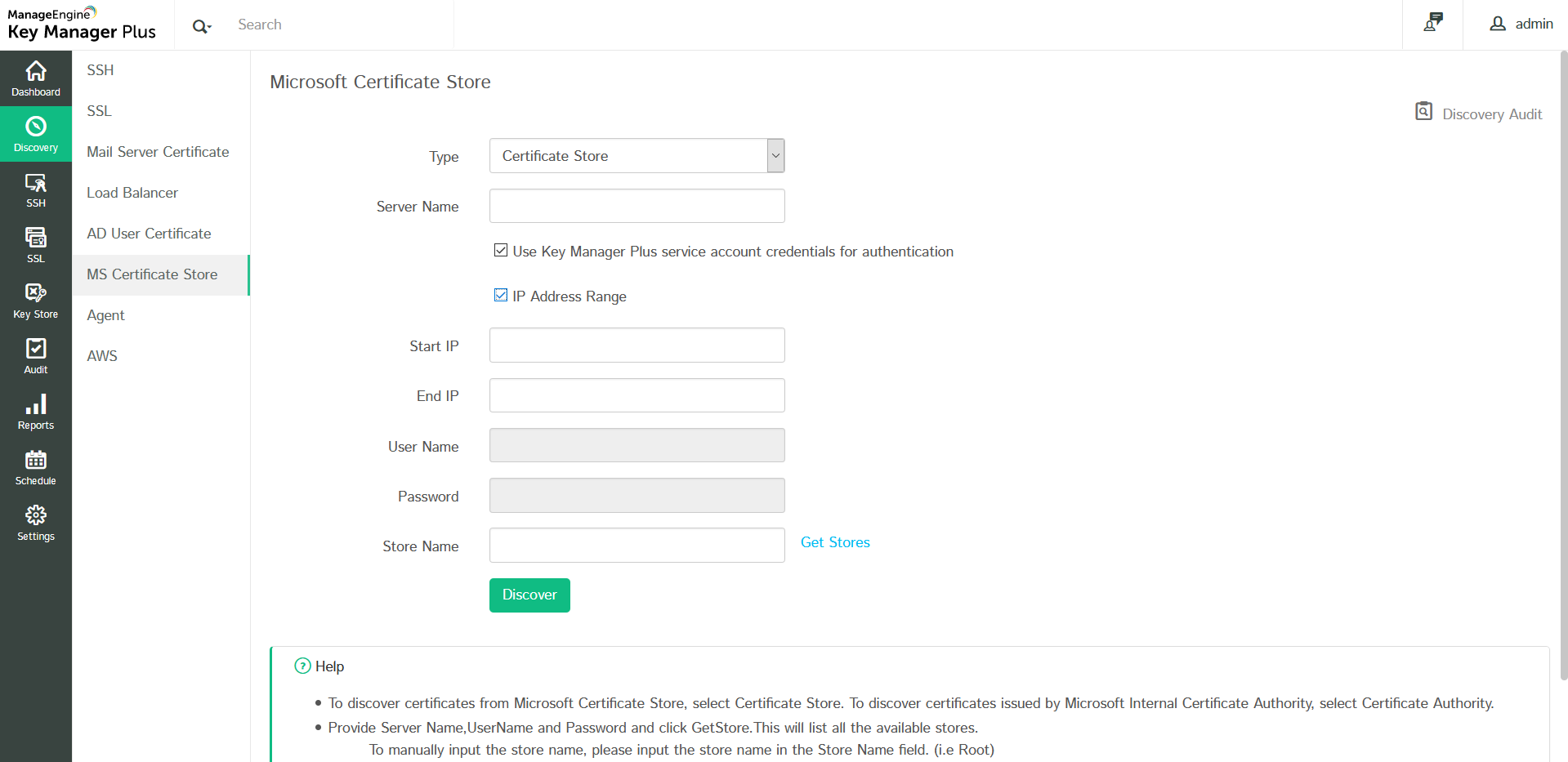
2.4 Manage Certificates from MS Certificate Store and Local CA
Key Manager Plus helps you request, acquire, discover, consolidate, track and manage certificates from MS Certificate Store and those issued by Local certificate authority. To begin managing certificates from Microsoft Certificate Store and Local Certificate Authority, start Key Manager Plus service using your domain administrator account. If you use a domain service account to run Key Manager Plus, make sure you have configured the account in your local admin group beforehand.
To import certificates from Microsoft Certificate Store and certificates issued by Local CA,
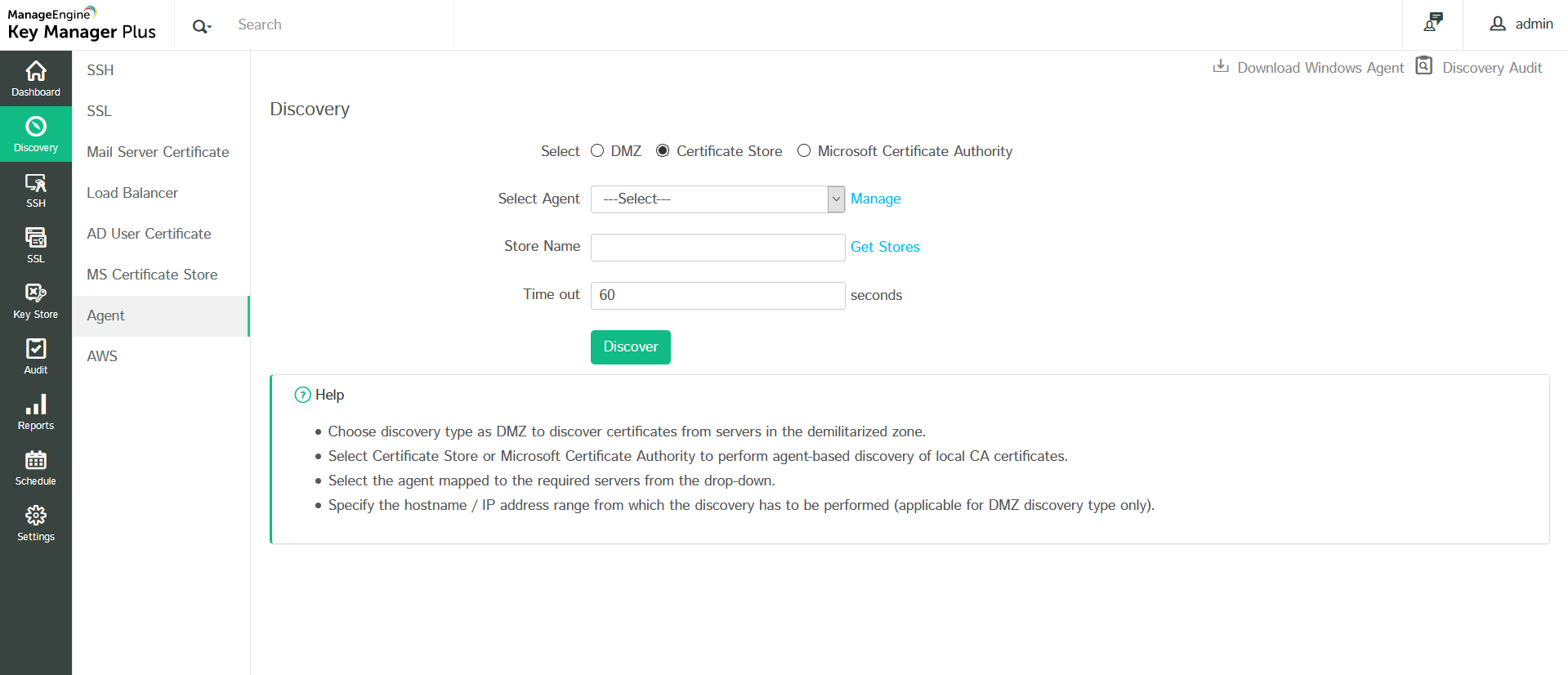
- Navigate to Discovery >> MS Certificate Store.
- To discover and import certificates issued by Microsoft CA alone, select Local Certificate Authority option from the drop down. You have options to filter the discovery - for instance, you can choose to exclude expired/revoked certificates and discover certificates based on issue date or certificate template.
- To discover all the certificates from MS certificates store, choose Certificate Store and enter the Server Name.
- To discover all the certificates from MS certificates store, choose Certificate Store.
- Select the checkbox to Use Key Manager Plus service account credentials for authentication or you can specify the other details such as the Name of the Windows domain controller machine and domain admin credentials.
- If you choose to Use Key Manager Plus service account credentials for authentication, you can select IP Address Range to mention the Start IP and End IP to discover the certificates.
- Specify the certificate Store Name from which the certificates are to be discovered and imported.
- i.e., Following format to be used while specifying the certificate store name:\\server_name\store_name
- e.g., server_name\Root (To discover certificates from trusted root certification authorities)
- e.g., server_name\My (To discover personal certificates)
- Or you can also click Get Stores to fetch the list of stores available in the Windows Domain Controller and choose the required certificate store that you want to discover.
- Click Discover.
- You can view the discovered certificates in SSL >> Certificates Tab.
Note: To discover certificates issued by a particular MSCA, select Type as Microsoft Certificate Authority from the drop-down, enter the Server Name, required credentials, and enter an MSCA name in the Microsoft Certificate Authority text box. Please note that this text box will be visible only if your Key Manager Plus server is installed in a Windows Server machine.
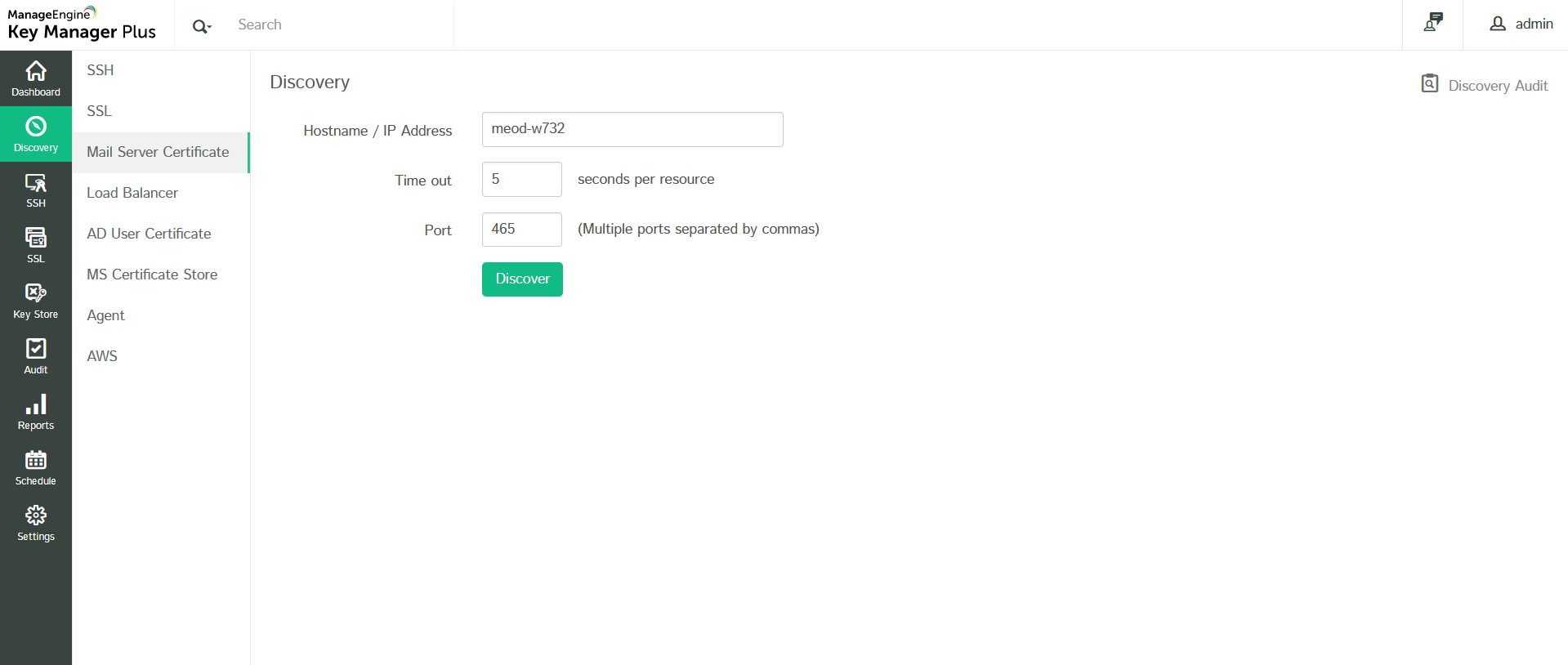
2.5 Discover Certificates from SMTP Servers
You can discover SSL certificates used by mail servers present in your network and consolidate them in Key Manager Plus' centralized certificate repository. To perform mail server certificate discovery,
- Navigate to Discovery >> Mail Server Certificate.
- Provide the Host Name or IP Address from which the certificate is to be discovered and specify the Port number. You can specify multiple port values by separating them with commas.
- Click Discover.
On successful discovery, the certificates are fetched from the specified resources and added to Key Manager Plus' repository.
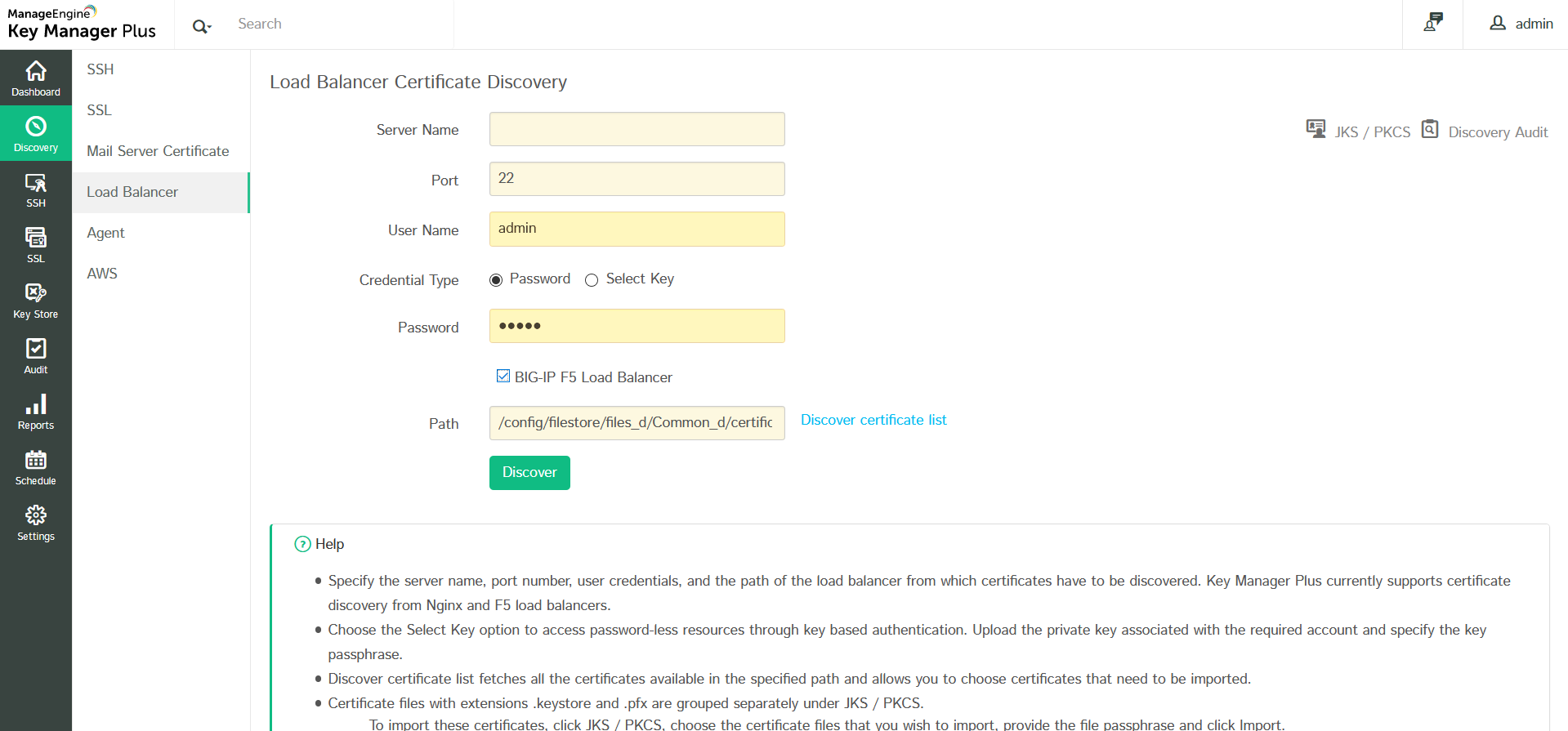
2.6 Discover SSL Certificates Deployed to Load Balancers
Key Manager Plus also allows you to discover SSL certificates deployed to load balancers within your network and consolidate them in its secure, centralized repository. Key Manager Plus currently supports certificate discovery from Linux based load balancers only (i.e., Nginx, F5 etc.,) and the process is tunnelled via SSH. To perform load balancer certificate discovery,
- Navigate to Discovery >> Load Balancer.
- Specify the Server Name, Port number, User Name and Password.
- You can opt for a key based authentication for password-less resources by choosing the Select Key option. Upload the private key associated with the required user account and specify the key passphrase.
- If the Load Balancer is of type BIG-IP F5, select the checkbox BIG-IP F5 Load Balancer.
- Once you have provided the user credentials, specify the Path in the server from which certificates have to be discovered.
- The Discover certificate list option fetches all the certificates available in the specified path and helps you choose certificates that you wish to discover and import.
- After choosing the list, click Discover.
- The certificates are successfully discovered and imported into Key Manager Plus' centralized certificate repository. You can view them from the SSL >> Certificates tab.
- Certificate files with extensions .keystore and .pfx require their passphrases to be provided in order to be imported into Key Manager Plus.
- These types of certificate files are not automatically imported into the certificate repository but are grouped separately under JKS / PKCS section (present in the top-right corner of the window).
- To import these certificates, click JKS / PKCS, and in the window that opens, choose the certificate file(s) that you wish to import and click Import from the top menu. In the pop up that opens, provide the file passphrase(s) and click Import.
The chosen certificate files are successfully imported and added to Key Manager Plus' certificate repository.
2.7 Discover SSL Certificates using KMP Agents
Key Manager Plus provides IT administrators the option to discover SSL certificates deployed across their network through agents. This functionality enables them to download and deploy Key Manager Plus agents to target systems, discover, and import certificates from those systems into a centralized certificate repository directly from the Key Manager Plus web interface. The connection between the Key Manager Plus server and the server(s) in which the agent is deployed is over HTTPS and is completely secure. Currently, Key Manager Plus agents are available only for Windows servers.
Performing certificate discovery through agents is helpful in the following scenarios:
- When the administrative credentials of the target server(s)—required to perform the discovery operation—are not available in the Key Manager Plus server.
- When certificates have to be discovered from servers that Key Manager Plus doesn't have direct access to—for instance, servers in demilitarized zone (DMZ). In such cases, the agent is usually installed in an intermediate jump server that has the permission to access the remote servers and pass on the required information to the Key Manager Plus server.
Steps to perform SSL certificate discovery through Key Manager Plus agent,
- Navigate to Discovery >> Agent.
- Choose the type of discovery you want to perform—domain based, Certificate Store or certificates issued by Microsoft Certificate Authority.
- Select the required agent from the drop down to perform the operation.
- If the agent is busy, wait and try again after sometime.
- For Microsoft CA discovery, you can choose to exclude expired / revoked certificates or perform discovery based on issue date or certificate template using the filters provided.
- Click Discover.
The certificates are discovered from the servers in which the agent is installed and imported into Key Manager Plus' certificate repository.
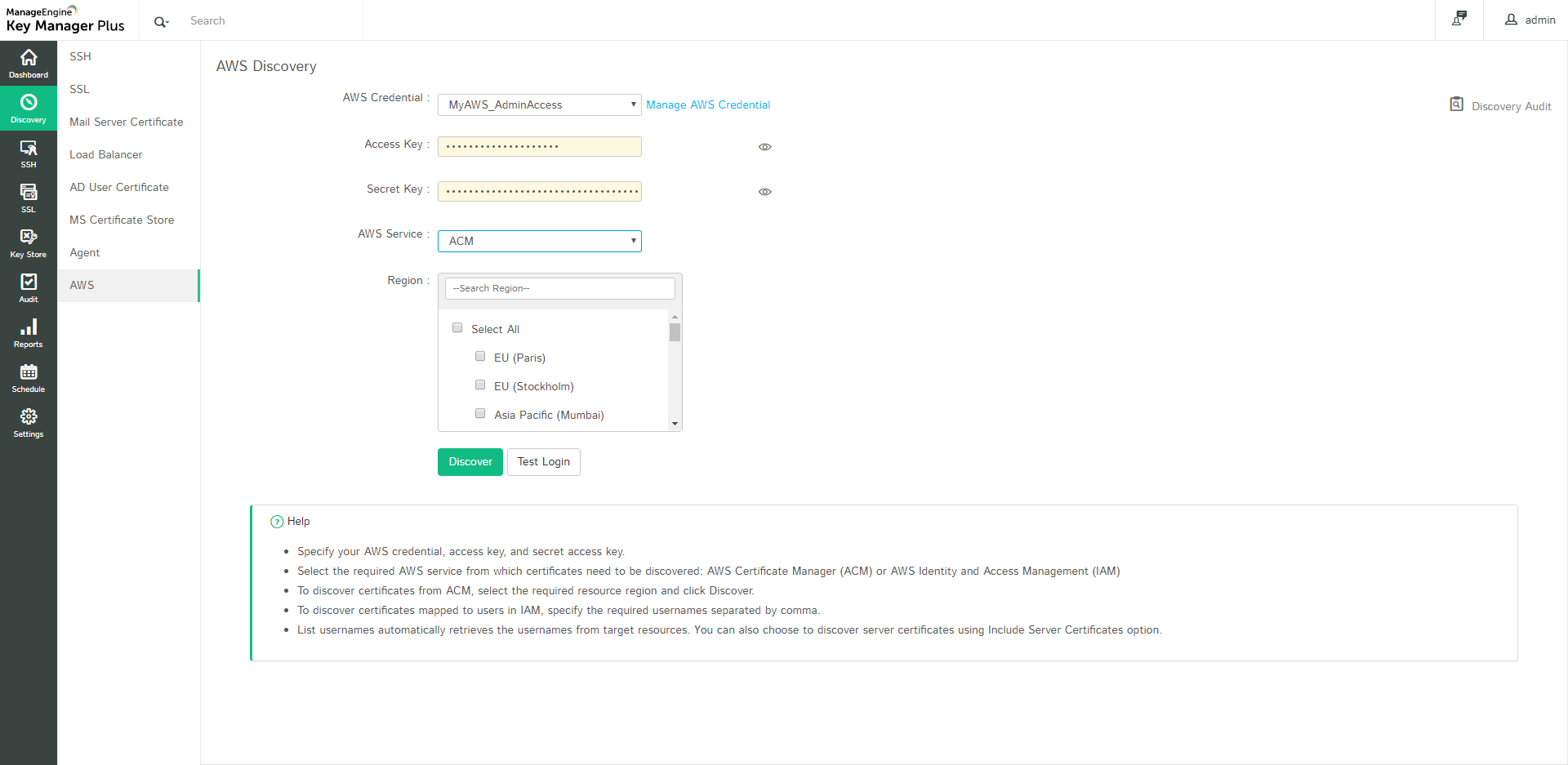
2.8 Discover SSL Certificates Hosted on AWS (ACM & IAM)
Key Manager Plus enables you to discover, import, and configure expiry notifications for SSL certificates hosted in the following Amazon Web Services: AWS Certificate Manager (ACM) and AWS Identity and Access Management (IAM).
Follow the steps below to discover and import SSL certificates from ACM / IAM into Key Manager Plus.
Step 1: Configure AWS credentials in Key Manager Plus
To add your AWS credentials in Key Manager Plus,
- Navigate to Discovery >> AWS >> Manage AWS Credential and click Add.
- In the Create AWS Credentials window that opens, provide the Credential Name, Access Key and Secret Key.
- Use the Test Login option and check if the login is successful. You will be notified if the login is successful
- Then click Save. The credentials are successfully saved in Key Manager Plus.
Step 2: Discovery and Import
- Switch to Discovery >> AWS tab.
- Choose the appropriate AWS Credentials from among the ones configured in Key Manager Plus or provide your Access Key and Secret Key.
- Choose the required AWS Service from which certificates need to be imported: ACM or IAM.
- To import certificates from ACM, select ACM under AWS service and choose the service Region.
- Click Discover.
- Certificates are discovered from resources in the selected region and imported into Key Manager Plus.
- To import certificates from IAM, specify the required AWS User Name(s) or use the List AWSUser Names option to retrieve the usernames. Choose the required usernames and click Discover.
- You can also choose to import server certificates for the corresponding AWS users by checking the Include Server Certificate option.
User certificates are imported into Key Manager Plus.
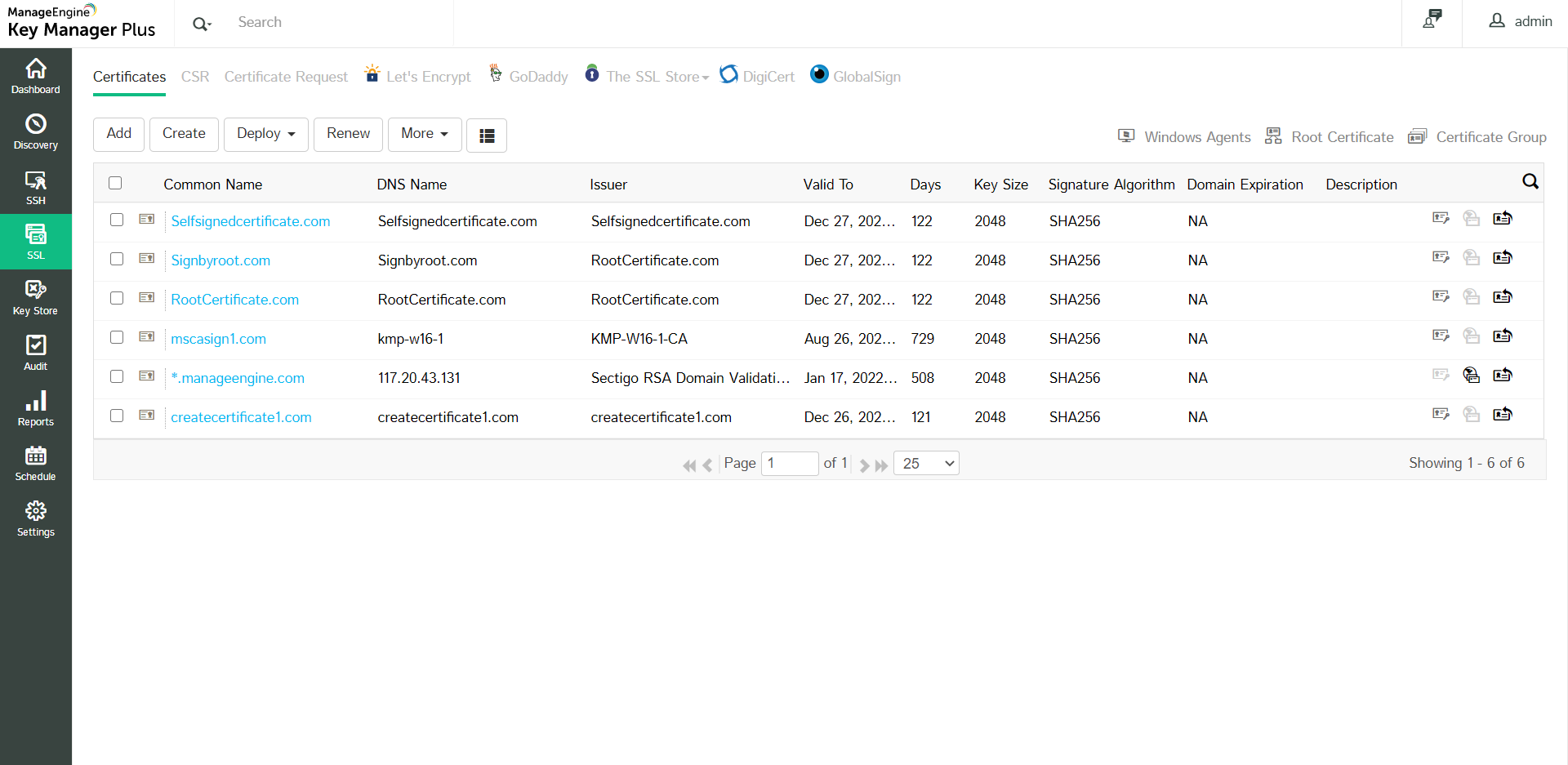
2.9 The Centralized Certificate Repository
All the discovered SSL certificates, those that are discovered manually as well as those discovered through scheduled discovery operations are automatically added to the centralized repository of Key Manager Plus. You can view these certificates from the SSL >> Certificates tab in the user interface.
2.10 Export Private Key / Keystore File
Key Manager Plus allows you to identify and export the private keys / keystore files of SSL certificates stored in the certificate repository. You can also export certificates in other formats such as PKCS12/PFX or PEM format. Click the Keystore icon ( ![]() ) enabled beside the certificates for which the private keys are managed using Key Manager Plus.
) enabled beside the certificates for which the private keys are managed using Key Manager Plus.
To export the private key or the certificate file:
- Navigate to SSL >> Certificates.
- Click the Keystore icon (
 ) beside the certificate for which you need to export the private key.
) beside the certificate for which you need to export the private key. - From the dropdown, choose from the following options as per your requirement:
- Export Keystore / JKS: The keystore file of the selected certificate will be downloaded.
- Export PKCS12/PFX: The selected certificate will be downloaded in the PFX format.
- Export PEM: The selected certificate will be downloaded in the PEM (Privacy Enhanced Mail) format.
- Export Private Key: The private key of the selected certificate will be downloaded.
- The corresponding certificate is downloaded in the selected format.
2.11 Track and Manage Various Certificate Versions
Sometimes, there occurs situations where you have to use different certificates on different end-servers for the same domain. Under such circumstances, it is necessary for you to track the usage and expiry of all these certificates individually even though they represent a common domain. Monitoring various such certificate versions manually is daunting and error-prone. Key Manager Plus helps you simultaneously track and manage the usage and expiry of various certificate versions from a single window.
To track certificate versions,
- Navigate to SSL >> Certificates.
- Click the Certificate History icon (
 ) present in the right corner of the table view, corresponding to the required certificate.
) present in the right corner of the table view, corresponding to the required certificate. - In the certificate history window that opens, choose the certificate version you wish to manage and click the Certificate Settings icon. Click Manage certificate.
- The particular certificate version is set for managing and Key Manager Plus starts tracking the usage and expiry individually for that version.
- Repeat the same procedure for all the certificate versions that you wish to manage.
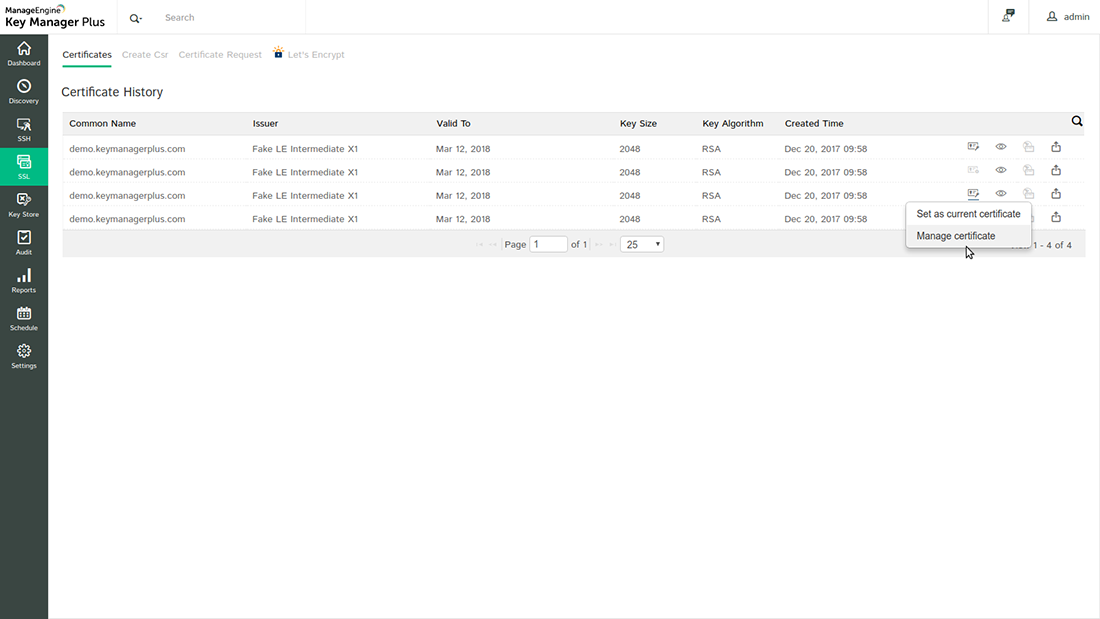
2.12 Update Servers with Latest Certificate Versions
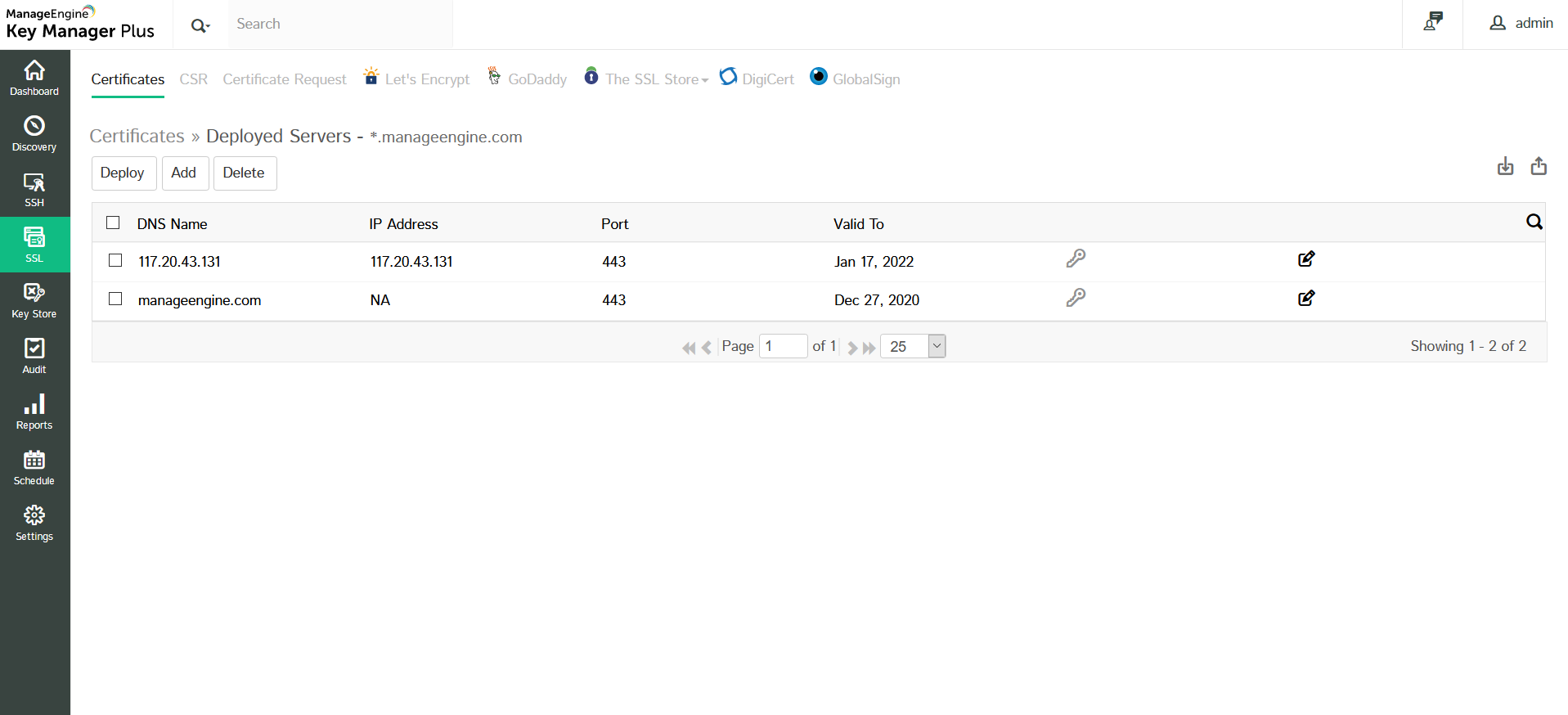
In case of wildcard certificates or single SSL certificate deployed to multiple servers, it is necessary to keep track of servers in which the certificate is deployed and also check if the latest certificate version is in use. Key Manager Plus helps you ensure this.
- Navigate to SSL >> Certificates.
- Click the Certificate History icon (
 ) corresponding to the required certificate
) corresponding to the required certificate - A window opens listing the various versions of the certificate. Ensure that the latest version of the certificate is set as the main certificate. If not, click the (
 ) icon beside the required version to set that version of certificate as main certificate in the Key Manager Plus repository.
) icon beside the required version to set that version of certificate as main certificate in the Key Manager Plus repository. - Then again, navigate to SSL >> Certificates tab and click multiple servers icon (
 ) corresponding to the required certificate.
) corresponding to the required certificate. - A window opens listing the servers in which the certificate is deployed along with other information such as IP address, port and certificate validity.
- If any of the servers listed has an older / expired version of the certificate, update it with the latest version immediately. Select the server and then click Deploy. Refer to the detailed deployment procedure here.
- Click Add to add a new server.
- In the pop-up that appears, mention the DNS Name, IP Address and Port.
- Click Save.
- Click edit icon corresponding to the required server to modify the server details and click Save.
Also, you can edit details pertaining to a particular certificate or delete irrelevant certificates by selecting the certificate and clicking the More dropdown.
3. Create Self-signed certificates
Key Manager Plus allows administrators to create their own self-signed certificates using Java keytool. These certificates are automatically imported into the Key Manager Plus repository on successful creation.
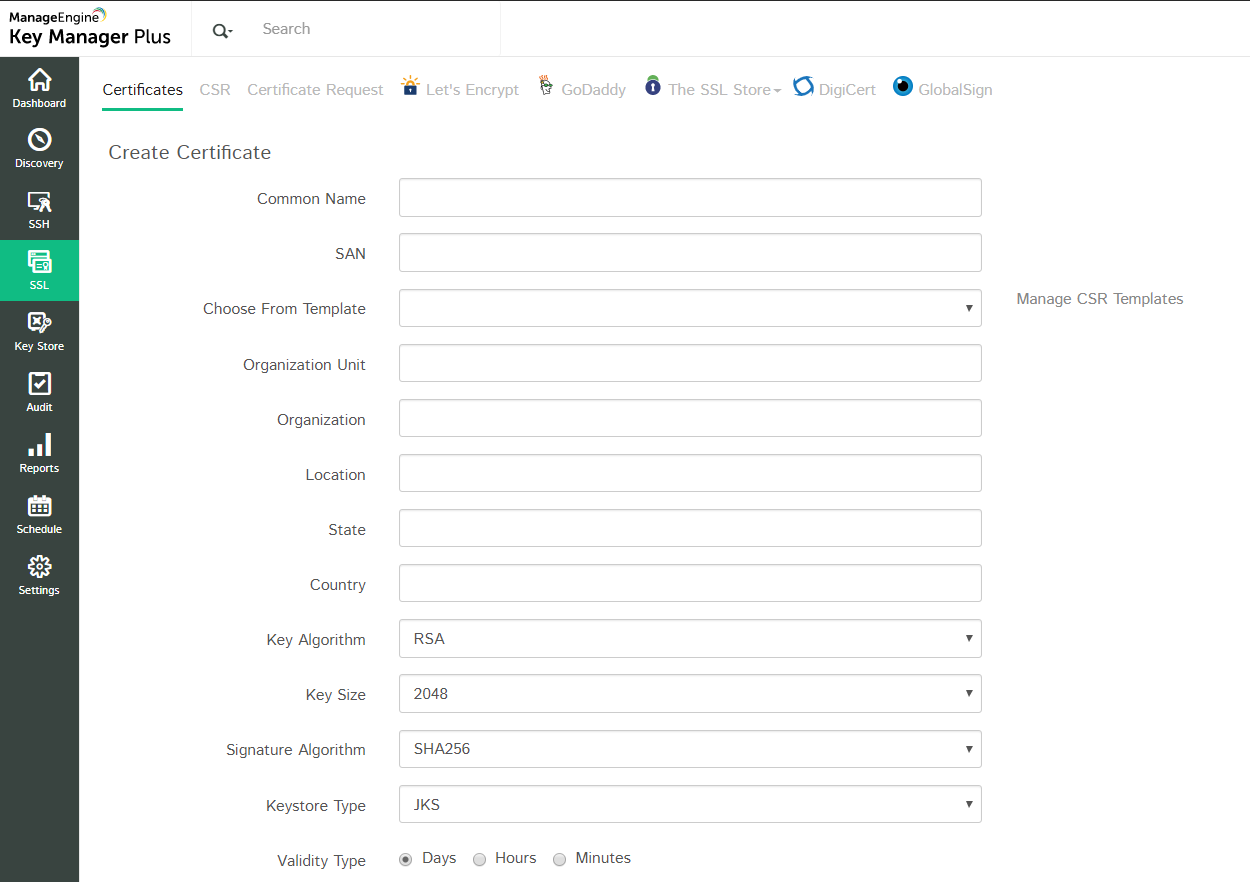
To create a self-signed certificate using Key manager plus:
- Navigate to the SSL >> Certificate tab in the GUI.
- Click the Create button.
- Enter the details of the organization and certificate validity, and select the Key Algorithm and Length, Signature Algorithm, and enter a key Store Password in the Create certificate tab.
- Choose the Validity Type as Days and specify the number of days for which the certificate will be valid.
- To create an ephemeral certificate with limited validity period, choose the Validity Type as Hours or Minutes and provide the validity period. The certificate will expire after the specified time (this option is applicable from build 5850 onwards).
- You can denominate the certificate to be generated as a root certificate by enabling the Generate root certificate check-box.
- To add optional properties to the new certificate, click Advanced Options to expand the menu. Here, there are two categories of options, Key Usage and Extended Key Usage. Select the required options to set the preferred flags for the certificate to denote the purpose for which the new certificate may be used. The Key Usage options include Non Repudiation, Digital Signature, Data or Key Encipherment, Server/Client Authentication etc. You can choose the properties and mark them as critical by selecting the Critical checkbox.
- Click the Create button. You will be redirected to the certificate window where the certificate content is displayed.
- You can copy the certificate content, or export the certificate to required email or system.
- Email – Select this check box to send the certificate file via email to the specified mail id.
- Export – Select this check box to export the file to your system.
- Both the options take effect once you click the Save button.
- Click the Save button to save the certificate in the Key Manager Plus repository, and export the certificate file, if opted in earlier step.
(Applicable from build 5920 onwards)
Note:
Apart from having a wildcard certificate name in the Common Name field, you can add the wildcard name in the SAN field while creating a self-signed certificate. With wildcard certificates, one can secure an unlimited number of subdomains for a registered base-domain.
For example, consider the base-domain zoho.com, a wildcard certificate for *.zoho.com can secure any-subdomain.zoho.com. The asterisk (*) is the wildcard that corresponds to any valid subdomain.

4. Generate CSRs
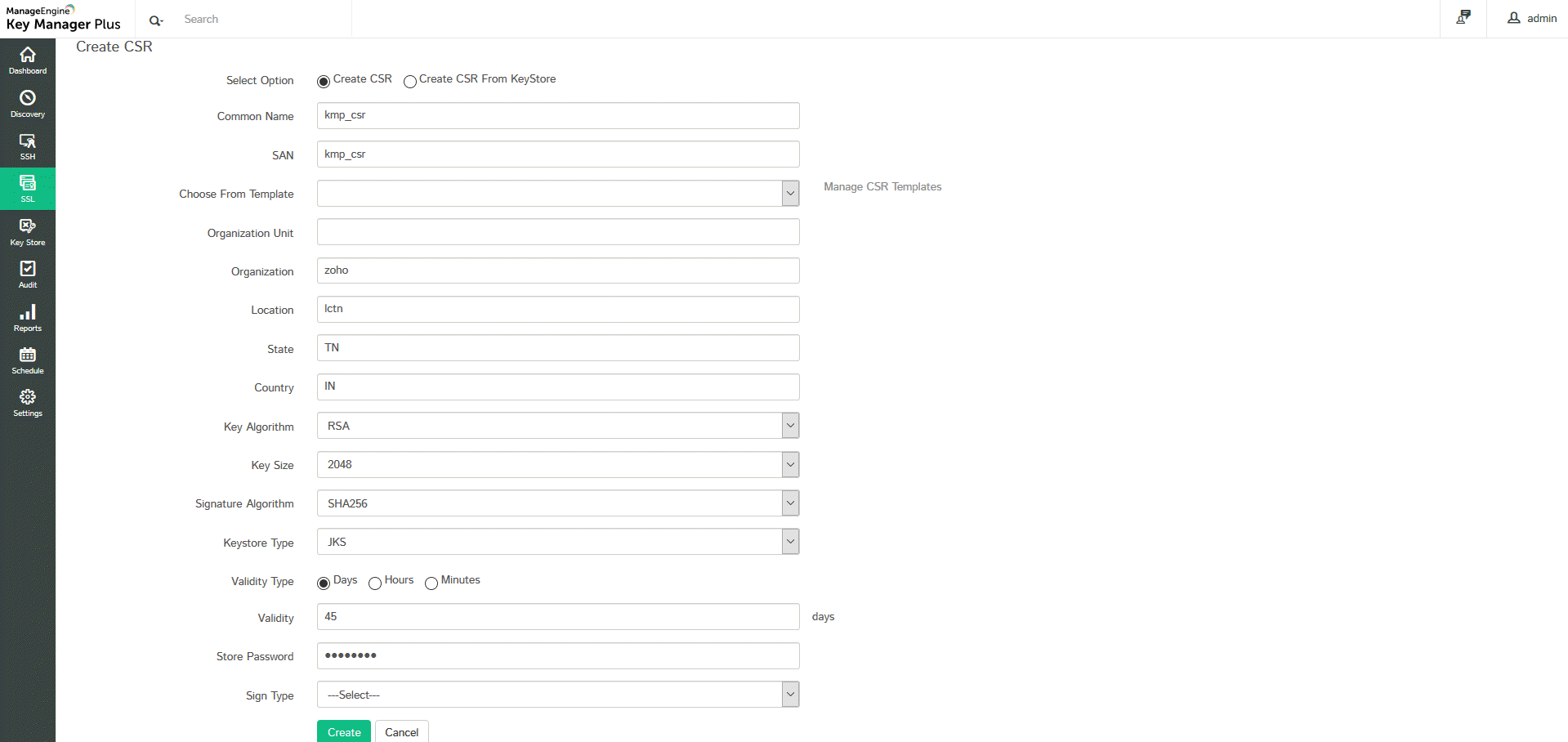
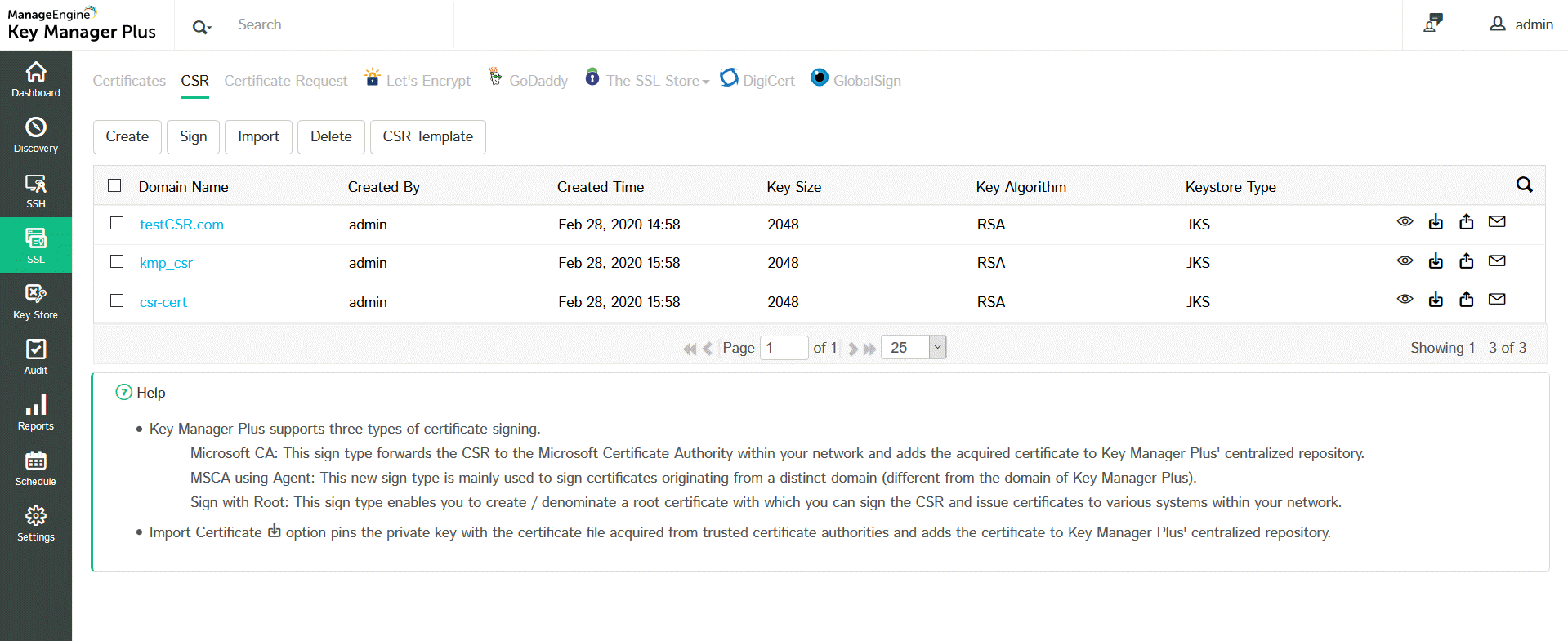
The following steps explain in detail on how to generate a CSR using java key tool from Key Manager Plus:
- Navigate to SSL >> CSR. You will see all the available CSRs in a list view along with their details such as Domain Name, Created By, Created Time, Key Size, Key Algorithm, etc.
- Click Create to generate a new CSR. In the form displayed, do the following:
- Choose between Create CSR manually or Create CSR from Keystore.You can also choose from a CSR template. Click the Manage CSR Templates link and choose one.
- If you choose to Create CSR from Keystore:
- Select the Keystore file by clicking Browse.
- Enter the Private Key Password and click Create.
- If you choose to Create CSR manually:
- Specify the required details such as Common Name, SAN, Organization Unit, Organization, Location, and State.
- Select the Key Algorithm, Key Size, Signature Algorithm, and Keystore Type.
- Choose a Validity Type (Days, Hours or Minutes) and mention the Validity.
- Enter the Store Password.
- Select the Sign Type and enter the required details.
- You can also sign your CSR later by not choosing the Sign Type now. To know more about signing the CSR later, click here.
- Click Create. You will be redirected to a CSR window where the CSR content is displayed.
- You have successfully created a CSR and it has been added to the list view.
(Applicable from build 5920 onwards)
Note:
Apart from having a wildcard certificate name in the Common Name field, you can add the wildcard name in the SAN field while creating a CSR. With wildcard certificates, one can secure an unlimited number of subdomains for a registered base-domain.
For example, consider the base-domain zoho.com, a wildcard certificate for *.zoho.com can secure any-subdomain.zoho.com. The asterisk (*) is the wildcard that corresponds to any valid subdomain.
4.1 Managing CSRs
- Show Passphrase: The show passphrase icon corresponding to every CSR allows administrators to view the keystore passwords of respective CSR files.
- Export: You can export and mail the CSR to a specified mail id by using the icons in the CSR displayed in the list view.
- Import: If you choose to import a CSR, click Import.A pop-up appears.
- Browse and Select a CSR file and Select a Key file.
- Enter the Private Key Password and click Import.
- Your CSR has been successfully imported and can be viewed in the list view.
- Key manager Plus automatically pins the certificate file with its corresponding private key and adds it to its centralized repository.
- Delete: To Delete a CSR, select the CSR you wish to delete and click Delete.
- In the pop-up that appears, click Ok.
- You have successfully deleted the selected CSR.
- CSR Template: Click CSR Template to add, delete or manage the templates. These templates after generated can be used while generating CSR’s.
Besides generating CSRs from Key Manager Plus, you can also upload CSRs generated from outside the application and track their statuses from Key Manager Plus using the Import option in the top menu.
5. Certificate Signing
Key Manager Plus provides the option to sign and issue certificates to all clients in your network either from your Microsoft Certificate Authority or using a custom root CA certificate that is trusted within your environment.
To request and acquire certificates from Local CA from Key Manager Plus, you have to initially generate a CSR, then get it signed from the local certificate authority using the steps mentioned below.
There are three ways to sign your certificates:
- MS Certificate Authority
- MS CA with agent
- Sign with Root
Navigate to SSL >> CSR.
5.1 Microsoft Certificate Authority
- Select the required CSR and click Sign from the top menu.
- Select the Sign Type as Microsoft Certificate Authority.
- Mention the Server Name that runs the internal CA and also the Certificate Authority name.
- Select the Certificate Template based on your requirement or select any of the pre-defined templates by clicking the Get Template link and click Sign.
The CSR is signed and the issued certificate can be viewed from SSL >> Certificates.
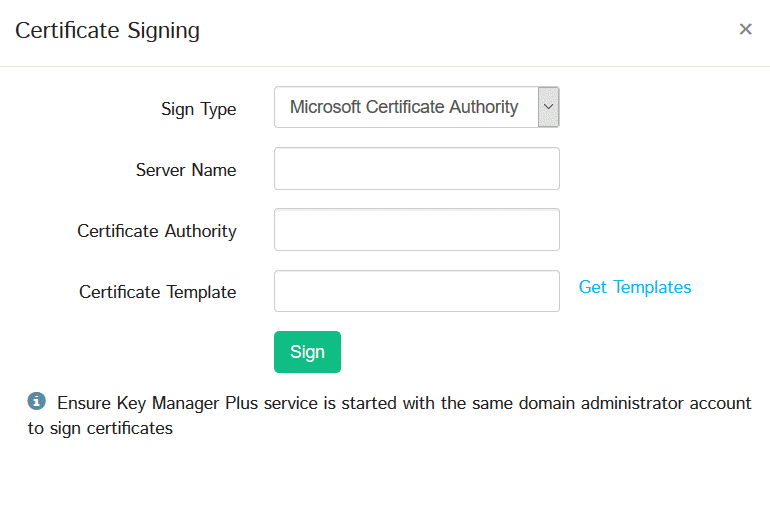
Notes:
- Start Key Manager Plus using your domain administrator account to begin management of certificates from Microsoft Certificate Store and those issued by your Local CA. If you use a domain service account to run Key Manager Plus, make sure that you have configured it in your local admin group beforehand.
- During MS Certificate Store discovery, Get Stores option will list all stores available in the local host if the Server Name field is left empty.
- For MS CA auto-renewal to take effect, the certificate(s) need to be of type Microsoft CA. For manually added certificates, the certificate type needs to be changed to Microsoft CA using Edit option from More top menu.
5.2 Microsoft CA with Agent
- Select the required CSR from the list view and click Sign from the top menu.
- In the pop-up that appears,
- Select the Sign Type as Microsoft CA with Agent.
- Select the Agent from the list available in the drop-down. You can also Manage the agent by clicking the link. To know more about managing the agent, click here.
- Specify the Certificate Template or click Get Template to get new templates.
- Mention the Agent Time out in seconds within which the agent should respond. If the agent doesn't respond within the timeout period, the operation will be audited as failed.
- Click Sign.
The CSR is signed and the issued certificate can be viewed from SSL >> Certificates.
5.3 Sign with Root
Key Manager Plus provides the option to sign and issue certificates to all clients in your network either from your Microsoft Certificate Authority or using a custom root CA certificate that is trusted within your environment. To Sign certificates with custom root CA follow the below steps:
- Create a custom root CA
- Sign certificates with the custom root CA
- Deploy the signed certificates to target systems
5.3.1 Create a Custom Root CA
To sign locally generated certificate requests with the root CA certificate, you have to initially create a custom root CA.
- Navigate to SSL >> Certificates tab.
- Select a certificate from the list view and click More >> Mark as Root.
The chosen certificate is successfully denominated as a root CA certificate and is listed under the Root Certificate tab. You can then use this certificate to sign locally generated certificate requests.
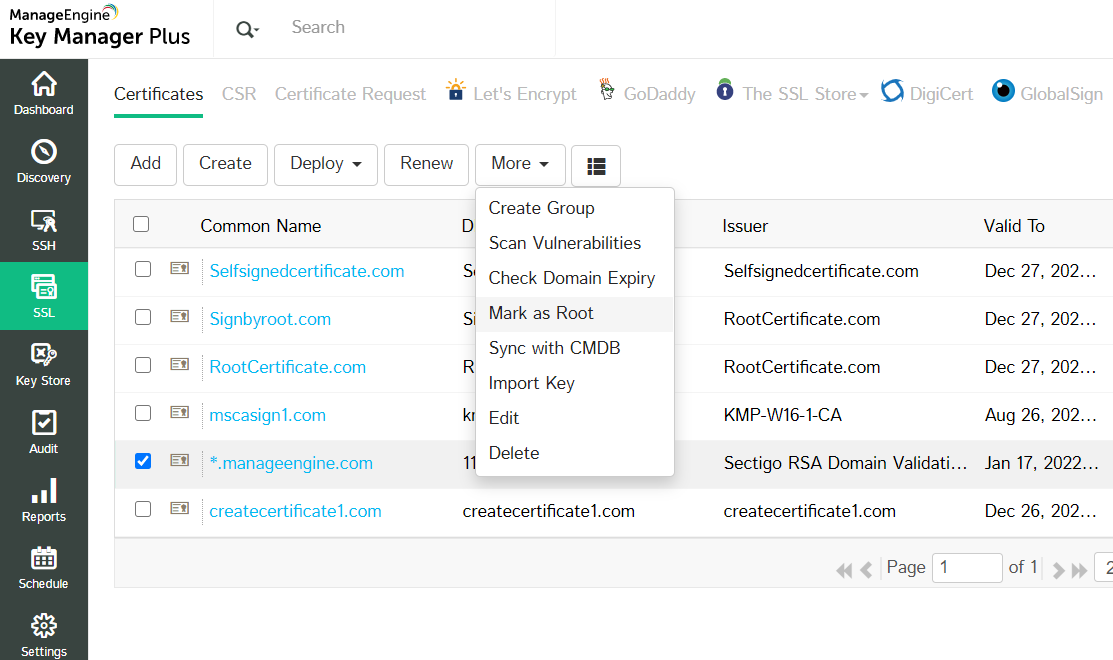
Note: You can also generate new root CA certificates from Key Manager Plus by enabling Generate root certificate check-box while creating a certificate from SSL >> Certificates >> Create option.
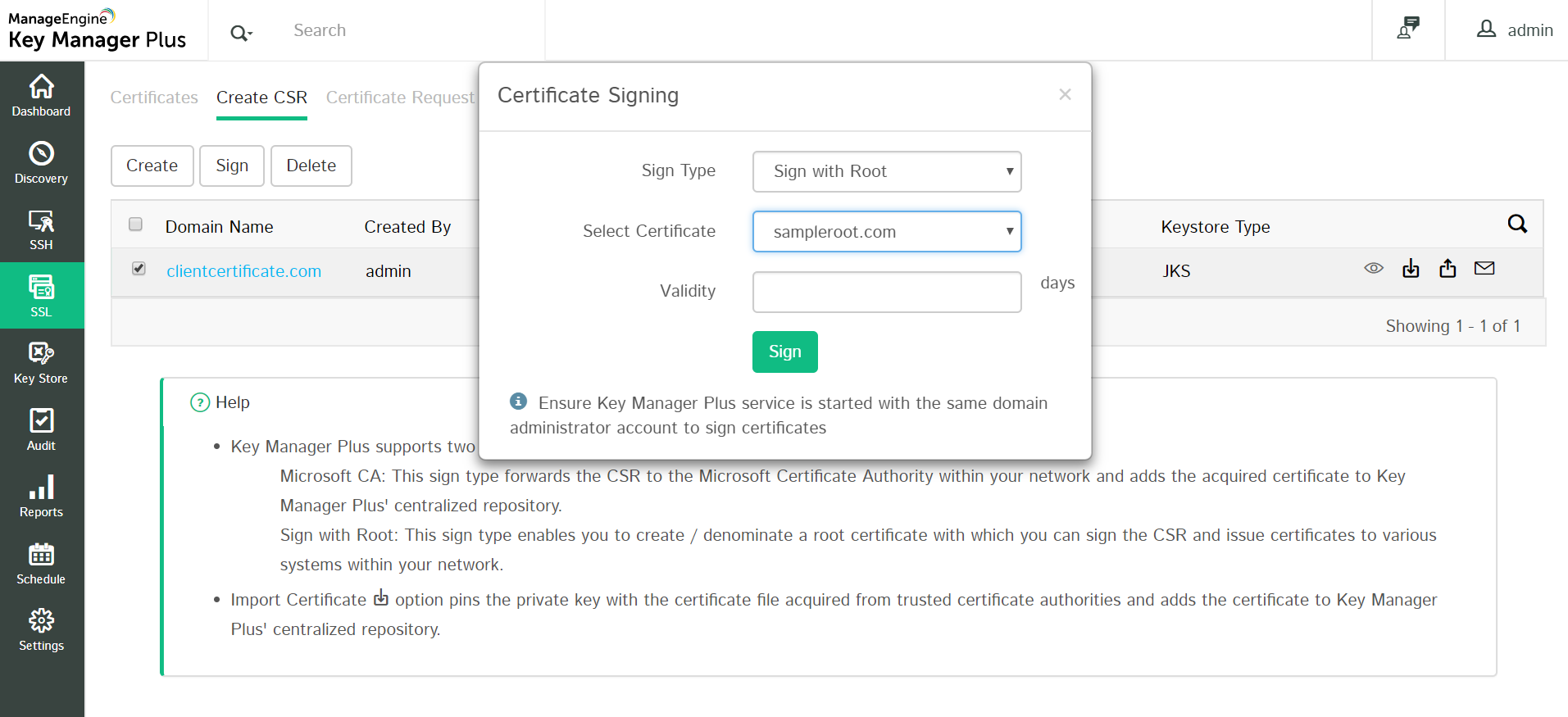
5.3.2 Sign Certificates with the Custom Root CA
To sign certificates with the custom root CA, generate a certificate signing request (CSR) and then sign it using the root certificate.
- Select the required CSR and click Sign from the top menu.
- Select the Sign Type as Sign with Root.
- Select the Root Certificate and mention the Validity in days and click Sign.
The CSR is signed and the issued certificate can be viewed from SSL >> Certificates.
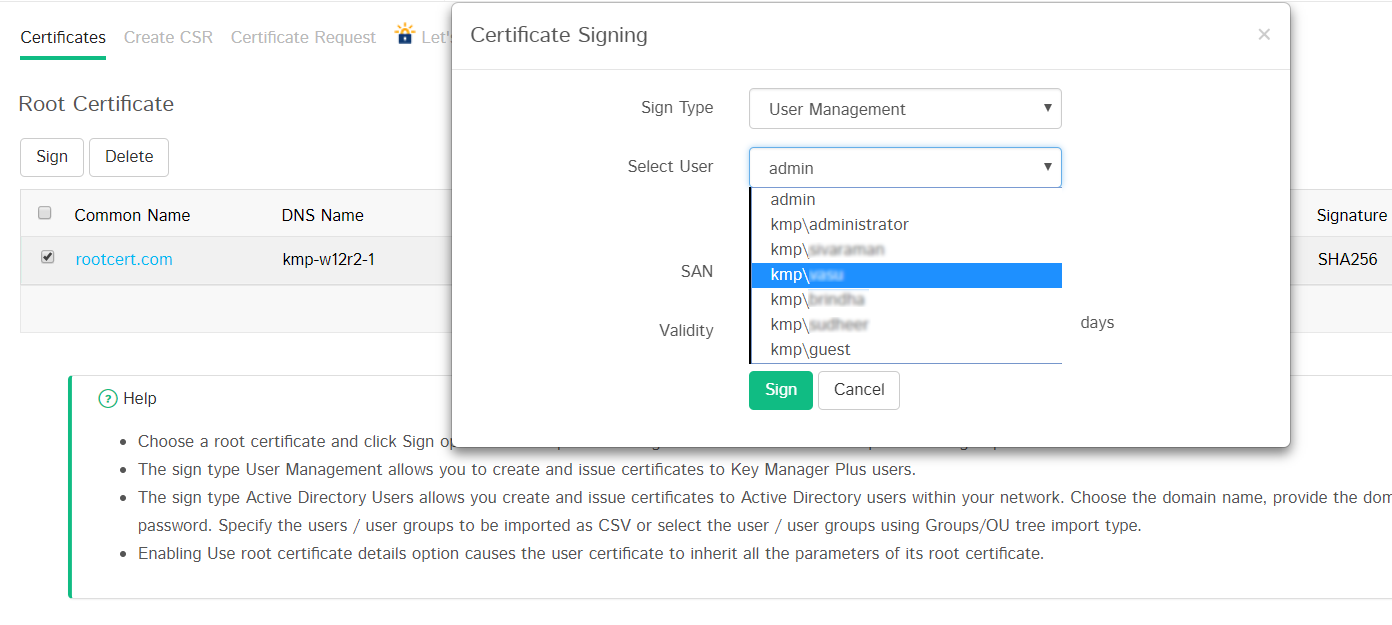
Also, you can use the root CA certificate to simultaneously generate and sign certificates to user groups in bulk directly from Key Manager Plus.
- Navigate to SSL and click Root Certificate on top-right corner of the window.
- Select the required root CA certificate and click Sign. In the pop-up that opens, choose the Sign Type, User / User Groups to which certificates have to be created and deployed, mention the SAN and Validity (in days).
- The sign type User Management allows you to generate and sign certificates for user accounts in Key Manager Plus.
- Select the User account for which you need to generate a certificate.
- By default, the user certificates inherit the same parameters as that of the root certificate. You can change it by unselecting the Use root certificate details option.
- After filling in the details, click Sign.
The certificate is signed and you can find listed in Key Manager Plus' certificate repository.
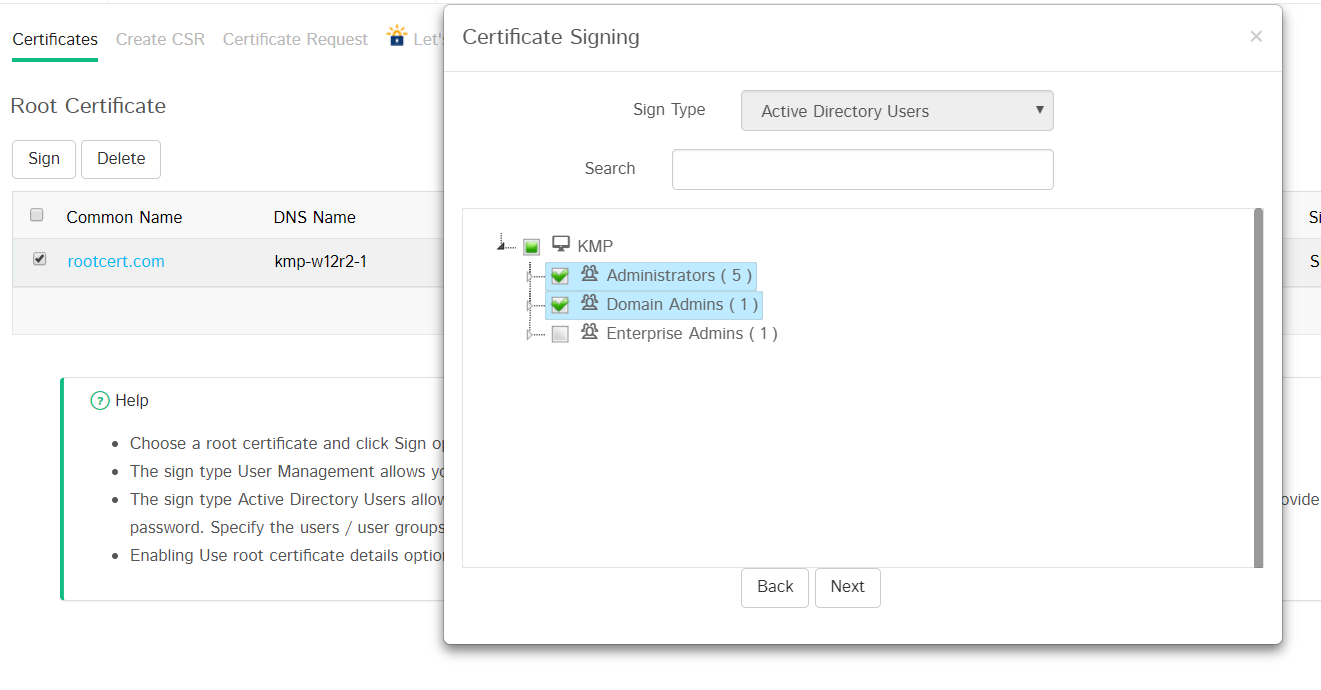
The sign type Active Directory Users allows you to generate and sign certificates to user accounts mapped to the Active Directory within your network environment.
- Select the Domain Name and provide the primary domain controller Address,User Name and Password.
- Choose import type Single and specify the user groups or use Groups/OU tree import type to choose the users or user groups for which certificates need to be created.
- After selecting the users, enter the certificate Validity in days. By default, the user certificates inherit the same parameters as that of the root certificate. You can change it by unselecting the Use root certificate details option.
- After filling in the details click Sign.
This will generate certificates for the selected users which will be listed in Key Manager Plus' certificate repository.
5.3.3 Deploy the Signed Certificate to Target Systems
After signing the certificate requests and obtaining the certificate, you have to deploy them to the necessary end-servers. Refer to this section of help for step-by-step explanation on certificate deployment.
Note: When signing certificates with custom root CA for web-applications, make sure all the browsers in your network are configured to trust the root CA certificate in order to avoid security error messages.
5.4 Auto Renewal
Certificates issued by Local CA can be renewed automatically from Key Manager Plus.
To enable auto-renewal of Local CA certificates,
- Navigate to Settings >> SSL >> Certificate Renewal.
- Enable MS Certificate Authority, MSCA using Agent or Self Signed and specify the Recurrence Time.
- Certificates that have already expired are auto-renewed and updated in the certificate repository.
- The certificates that are due to expire in the number of days mentioned in the Days to Expire field will also be auto-renewed.

6. Certificate Renewal
The Certificates tab in Key Manager Plus is a centralized console where all types of SSL certificates such as Self Signed, Root Signed, Microsoft CA Signed, certificates issued by third-party CAs etc., are consolidated and displayed. Through the Renew option, these certificate types can be renewed in the Certificates tab directly. For certificates issued by third-party CAs, the renewal will be initiated and redirected to the respective CA's tab. To proceed further, follow the below steps:
- Navigate to SSL >> Certificates.

There are three types of certificate renewal:
- Self Signed certificate renewal
- Root Signed certificate renewal
- Microsoft CA Signed/Signed with Agent certificate renewal
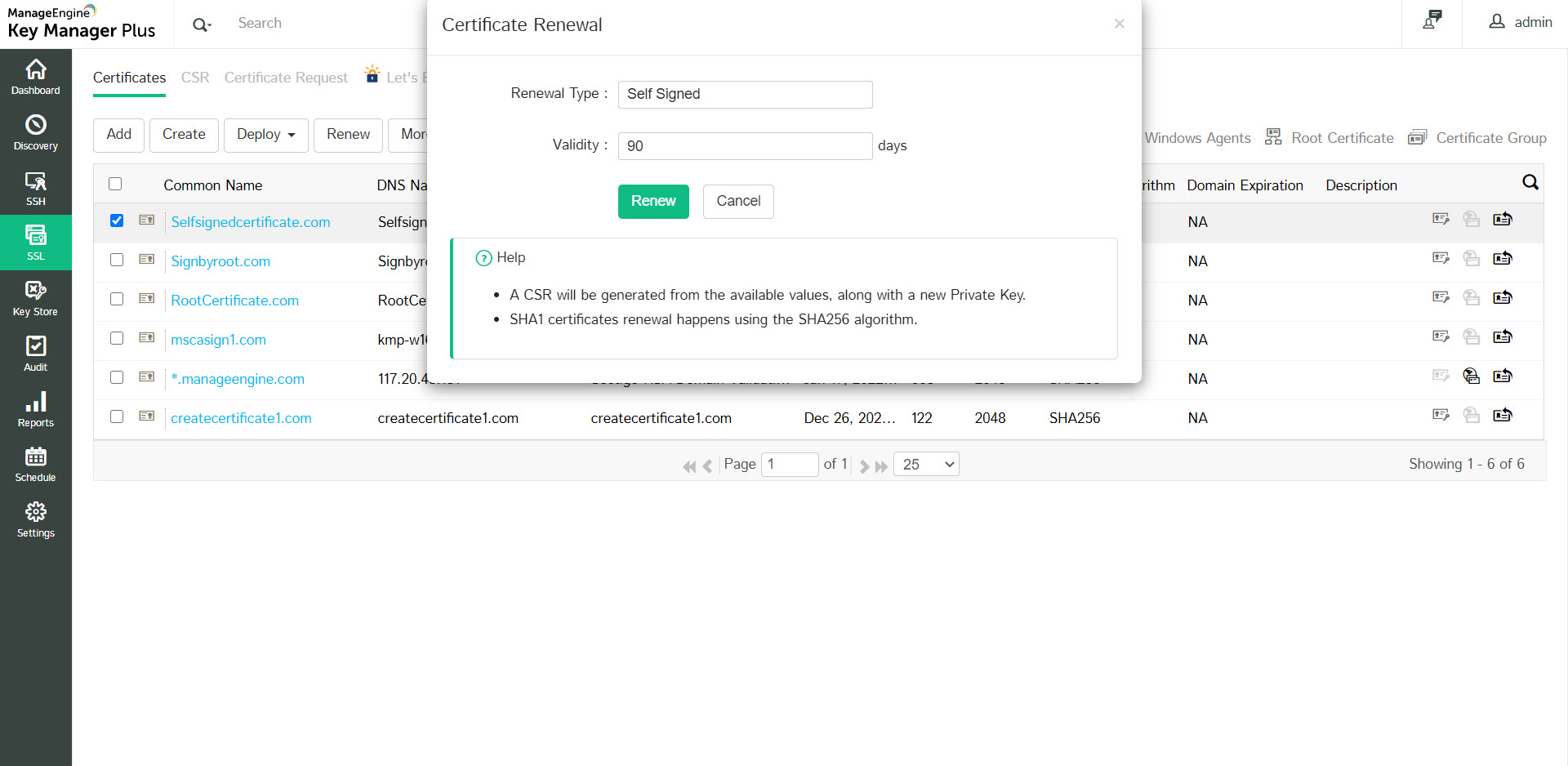
6.1 Self Signed Certificate Renewal
To renew a Self Signed certificate, follow the below steps:
- Select a Self Signed certificate and click Renew at the top.
- The renewal type will be Self Signed by default.
- Specify the number of days for which the certificate shall be valid in the Validity field. Click Renew.
The certificate will be renewed successfully and the Valid To date will change according to the new validity period specified.
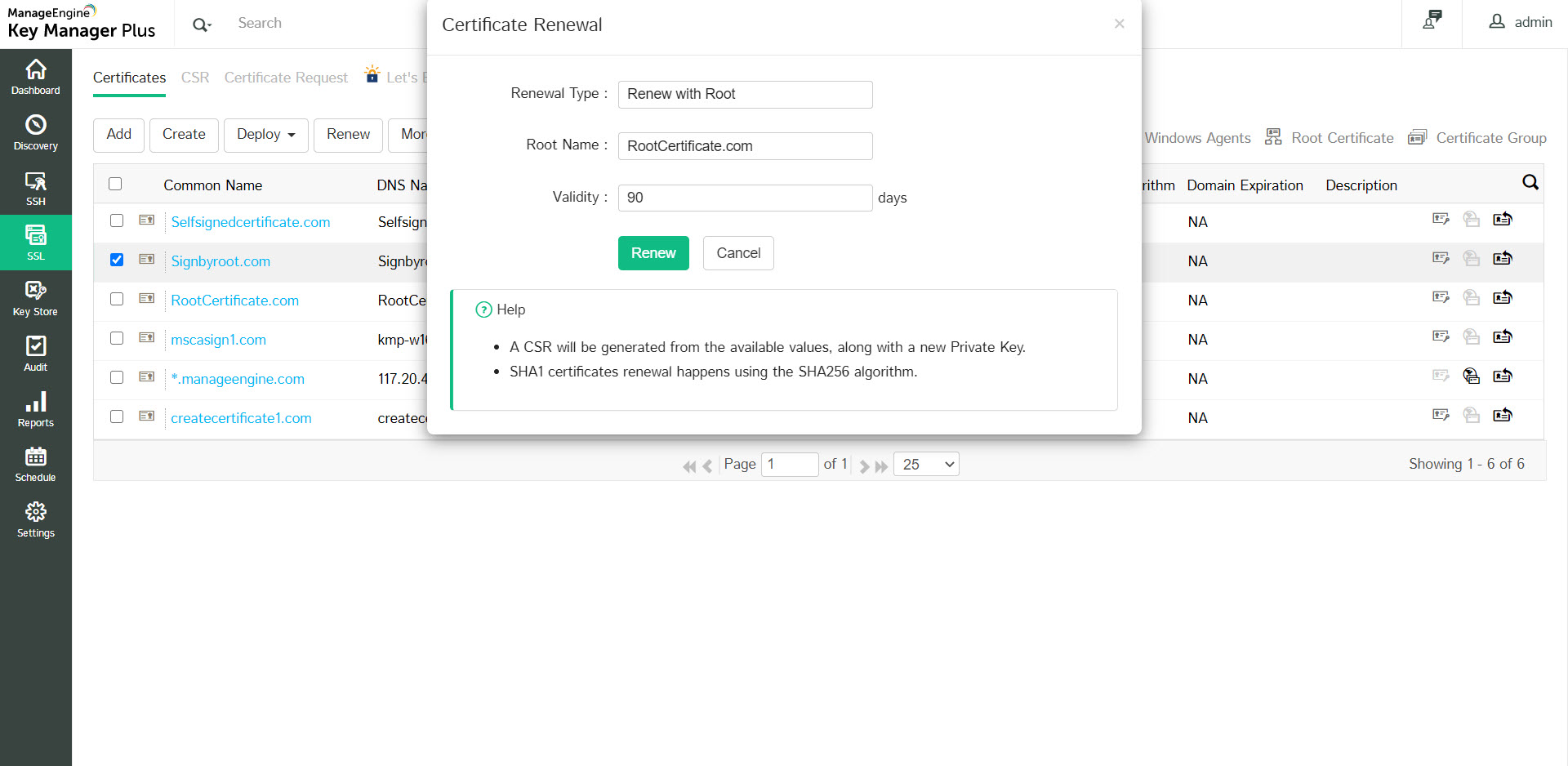
6.2 Root Signed Certificate Renewal
To renew a Root Signed certificate, follow the below steps:
- Select a Root Signed certificate and click Renew at the top.
- The renewal type will be Renew with Root by default and the Issuer name will be autopopulated in the Root Name field.
- Specify the number of days for which the certificate shall be valid in the Validity field. Click Renew.
The certificate will be renewed successfully and the Valid To date will change according to the new validity period specified.
6.3 Microsoft CA Signed/Signed with Agent Certificate Renewal
To renew a Microsoft CA signed certificate, follow the below steps:
- Select a Microsoft CA Signed certificate and click Renew at the top.
- Attributes such as Renewal Type, Server Name, Certificate Template, Certificate Authority will be autopopulated from the certificate details. The Server Name is the name of the Microsoft CA server which signed the certificate. Certificate Authority is the CA service that runs in the specified Microsoft CA server.
- For certificates signed by Microsoft CA directly or using the KMP agent, validity days will be taken from the Microsoft CA server and therefore it cannot be entered manually during renewal. These type of certificates will be renewed only till the date specified in the the Microsoft CA server.
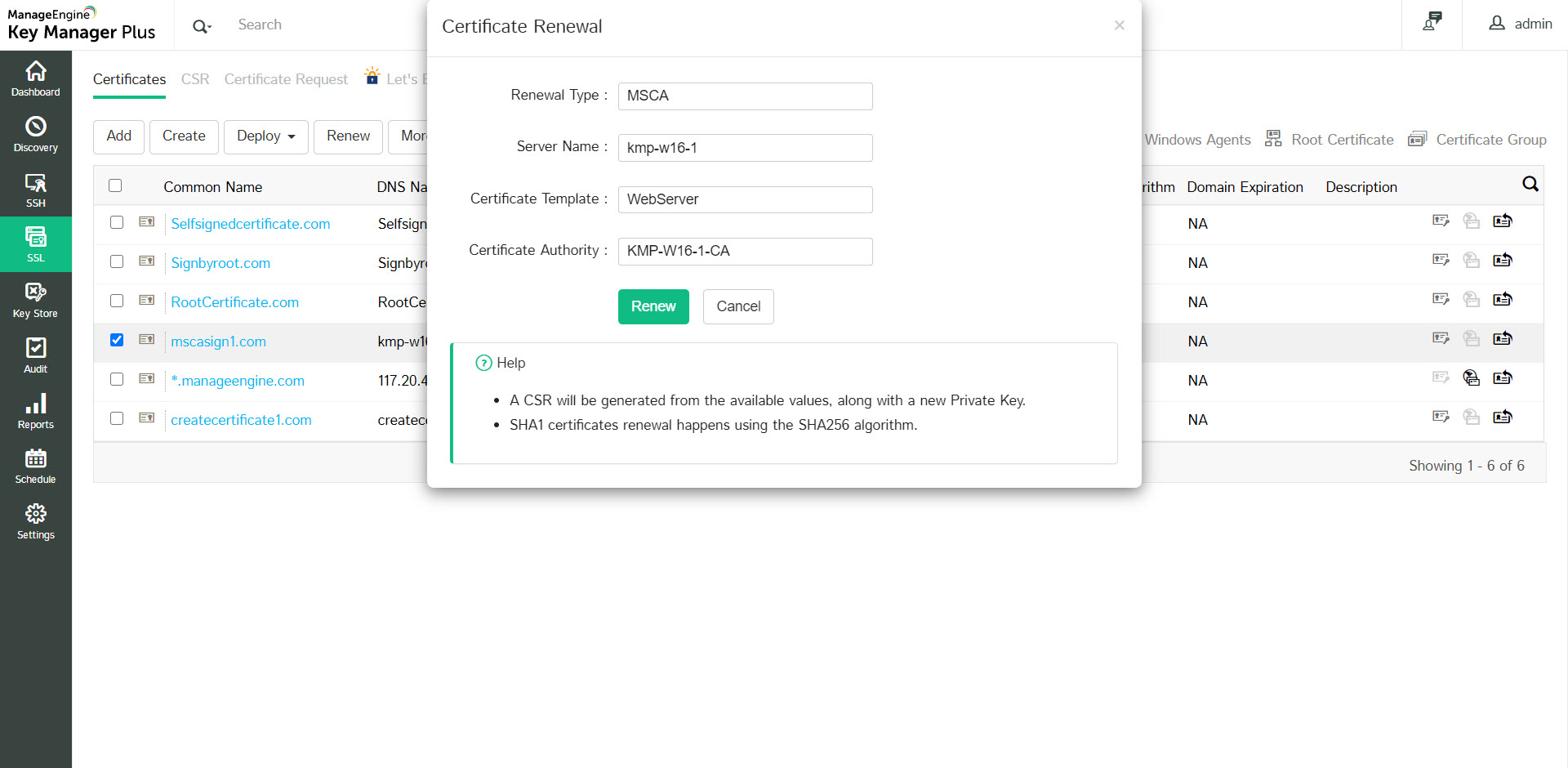
In addition to the above types, third-party CA signed certificates can also be renewed using this renewal option. Follow the same procedure to initiate renewal and Key Manager Plus will redirect the renewal request to the respective third-party CA. Click here to learn how to set up auto-renewal for certificates in Key Manager Plus.
- Certificates that do not have a private key cannot be renewed.
- During the renewal process, a CSR will be generated from the available values, along with a new Private Key.
- SHA1 certificates will be renewed using the SHA256 algorithm.
7. Import Certificates
To import the certificates in your network:
- Navigate to the SSL >> Certificates tab and click the Add button.
- Click the appropriate radio button in the Add certificate window.
- File Based – Browse and import the required certificate file directly from your system.
- Certificate content based – Copy the content of the required certificate file and paste it in the text box.
- KeyStore based – Import all individual certificates available in a keystore simultaneously. Upload the required Keystore file and enter its corresponding password (if any).
- Click Add.
8. Delete Certificates
You can delete the certificates that are currently not in use. To delete a certificate from Key Manager Plus repository:
- Navigate to the SSL >> Certificate tab.
- Select the certificates to be deleted and click the Delete button.
9. Certificate Requests
The certificate request workflow is as follows:
- Add certificate request
- Close certificate request
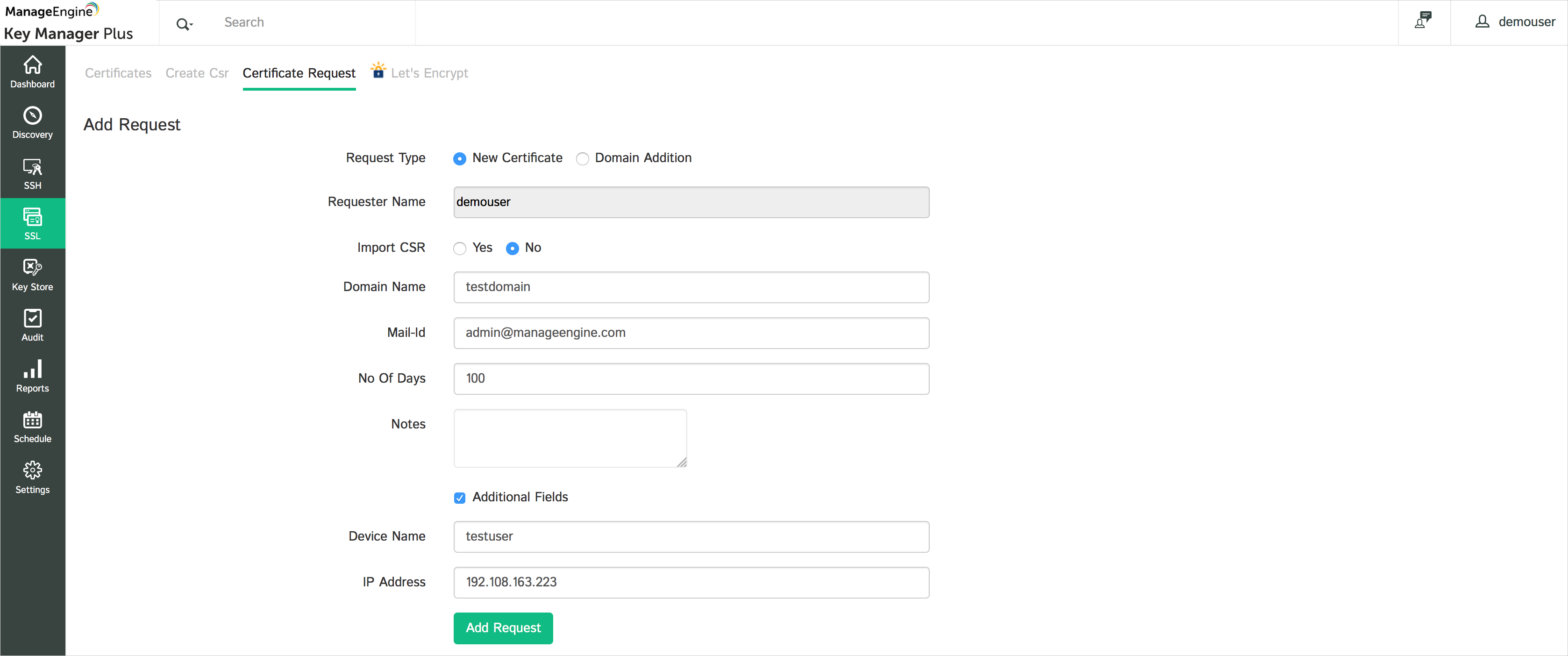
9.1 Add Certificate Request
To add requests for new certificates or addition of sub-domains to existing certificates, in Key Manager Plus:
- Navigate to the SSL >> Certificate request tab and click the Add Request button.
- Select the type of request – Certificate or domain addition.
- New Certificate – Attach a CSR to your request (optional) and a domain name for the new certificate.
- Add domain – Enter the name of the new domain and select a parent domain from the certificates added to the Key Manager Plus repository.
- Enter the Email-Idto which you would like to send the request and specify the certificate validity period. These mail addresses can be that of an administrator, an intermediary who handles certificate requests, or even your help desk software to raise the certificate request as a ticket.
- For eg., admin@keymanagerplus.com, help-desk@manageengine.com.
- Select Additional fields to add additional information such as device name and IP address
- Click Add Request to add it to the list of request in the Certificate Request tab and to send the same to the specified email addresses.
9.2 Certificate Request Status
A certificate request is in either of the following statuses.
- Open
- Closed
When a certificate request is raised, it is automatically elevated to the Open State. The request details can be viewed from the SSL >> Certificate request tab, on clicking the domain name of the request.
9.3 Close Certificate Request
To terminate the certificate request life-cycle:
- Navigate to the SSL >> Certificate Request tab in the GUI.
- Click the Open status link in the right corner of the table against the required open request process.
- In the Close Request window, add an optional Annotation, and attach the Certificate issued (optional), specify the Email-ids of users to whom the certificate is to be sent and click the Save & Close button. Once you click the button, the request is automatically moved to the Closed state.
- If a SSL certificate is attached while closing the request, the certificate is automatically imported to the Key Manager Plus repository.
- Also, the issued certificate is e-mailed to the user who raises the request, the user who closes the request and also to those e-mail ids specified at the time of closing the request.

10. Control Expiry Notification Schedule
You can customize the periodicity of notifications you receive when a certificate is about to expire. To customize the notifications:
- Navigate to Settings >> Notifications tab in the GUI.
- Select the Certificates expire after checkbox and the number of days before the expiry of certificate within which you should start receiving notifications.
- Select the Email or Syslog checkbox and enter appropriate details.
- Click the Save button.
Note: You will receive notifications every day after the selected date before the expiry of a certificate. For instance, if a certificate is about to expire in the last week of a month, and you select the Notify if SSL certificates are expiring within 7 days option, then, you will receive a notification that your certificate is about to expire every day of the week before the expiry of the certificate.
11. Track Domain Expiration through WHOIS Lookup
Apart from tracking certificate expiration, Key Manager Plus also helps administrators keep a tab on their expiring domain names through an automated WHOIS look up. The domain expiration details fetched through the lookup are displayed in SSL >> Certificates tab against its corresponding SSL certificate. Also, administrators can choose to receive timely email notifications of their expiring domains by configuring it in Settings >> Notification tab.
How does the WHOIS lookup work?
Fetching domain expiration details requires a two-stage lookup to WHOIS servers from Key Manager Plus. The first lookup provides the details of the WHOIS server with which the domain was registered by its domain registrar. The second lookup provides information about the domain such as owner details, expiration date etc., All these operations are automated the from Key Manager Plus' interface.

Note: Connection to WHOIS servers requires the use of Port 43. Ensure that port 43 is open in your environment, else the connection would fail and Domain Expiration will be marked Not Available (NA) in the Certificates tab.
12. SSL Certificate Group
Key Manager Plus allows you to organize SSL certificates into various logical groups and execute actions in bulk on the groups.
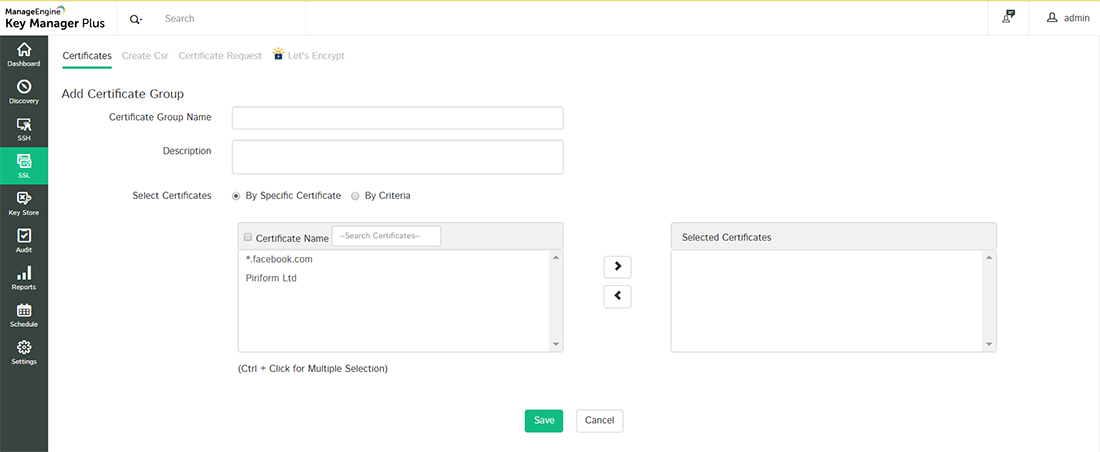
12.1 Create Certificate Groups
To create a certificate group,
- Click the Certificate group icon in the top-right corner of the SSL >> Certificates tab.
- Click Add Group. You will be directed to the Add certificate group window.
- Provide a name for the certificate group and an optional description. Exercise caution while providing the name since it cannot be changed later.
- You can choose certificates to be added to a group in 2 ways:
- By specific certificate - Select the certificates to be added to the group individually and click Save.
- By criteria - This serves as a dynamic method of grouping certificates. You will specify various criteria based on which the group will be created. Here, you can choose certificates based on various criteria such as issuer, common name, key algorithm, key size, key length etc. The additional fields that are added will also be displayed in the list. You can filter the search in a fine-grained manner based on conditions such as "equals" or "does not equal", "contains" or "does not contain", "starts with" or "ends with". Click the Matching certificates button at the bottom-right corner to see the corresponding certificates. Click Save. The certificate group is created. To know more about additional fields, click here.
Note: If you choose to group certificates based on criteria, the conditions will be applied to certificates discovered in the future and they will automatically be added to groups that match the criteria.
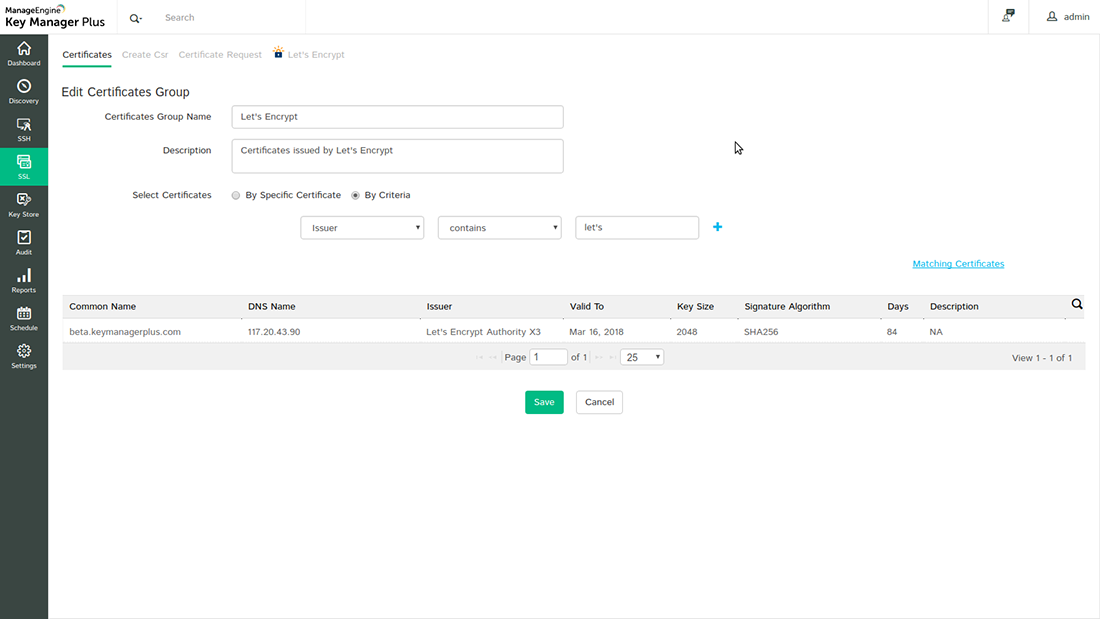
12.2 Edit Certificate Groups
To make changes to existing certificate groups,
- Click the certificate group icon on the top-right corner of the SSL >> Certificates tab.
- Click the edit icon present in the right corner of the table view.
- You can change the certificate selection type, edit the certificates present in a group or add, modify or delete the filters applied to a group.
- Once you update the changes and save them, a pop up message will be displayed confirming the updates.
Note: The certificate group name cannot be modified. However, you can add or modify the list of certificates in a group or the description.
12.3 Delete Certificate Groups
To delete a certificate group,
- Click the Certificate group icon on the top-right corner of the SSL >> Certificates tab.
- Select the groups that you want to delete and Click Delete.
- A pop-up window will appear asking you to confirm the action.
- Click Ok and the selected certificate groups will be deleted.